Understanding G Network Setup for Multi-Factor Authentication
As the digital landscape continues to evolve, the importance of implementing multi-factor authentication (MFA) in network security has become increasingly crucial. G Network, a robust and secure platform, offers a comprehensive setup for MFA, providing an additional layer of protection against unauthorized access and cyber threats.
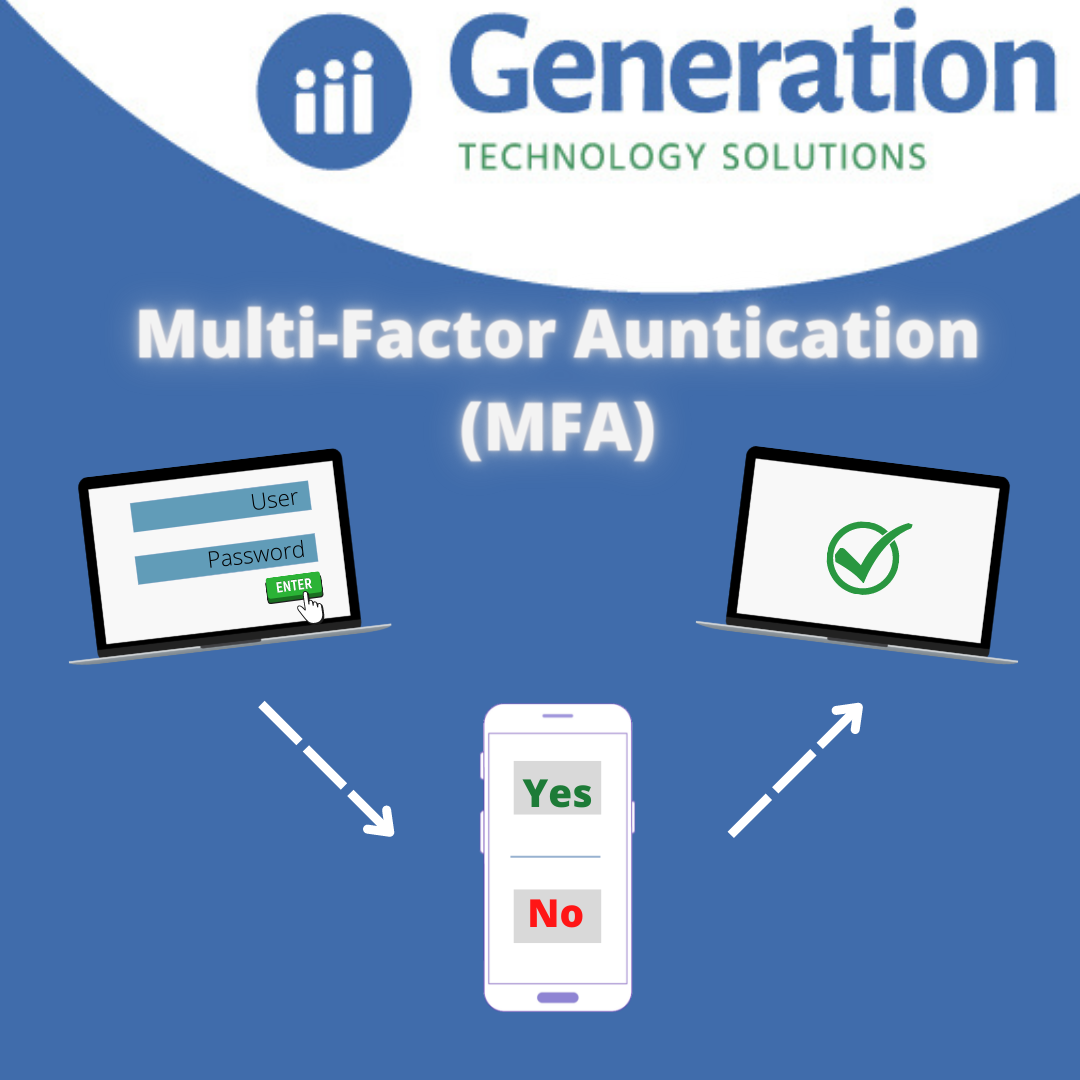
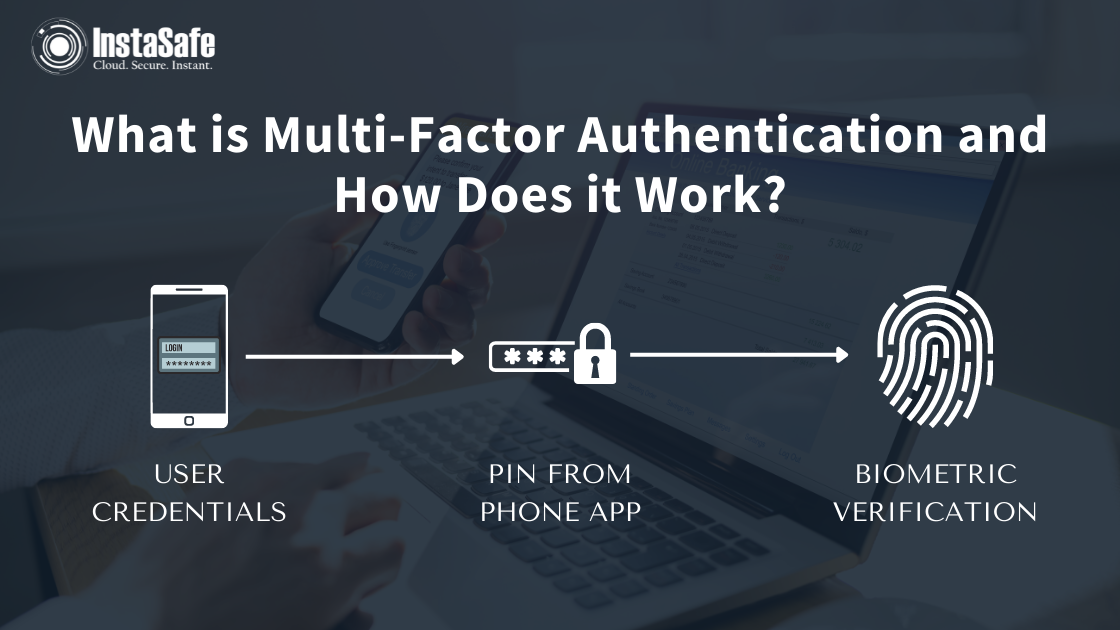
What is Multi-Factor Authentication?
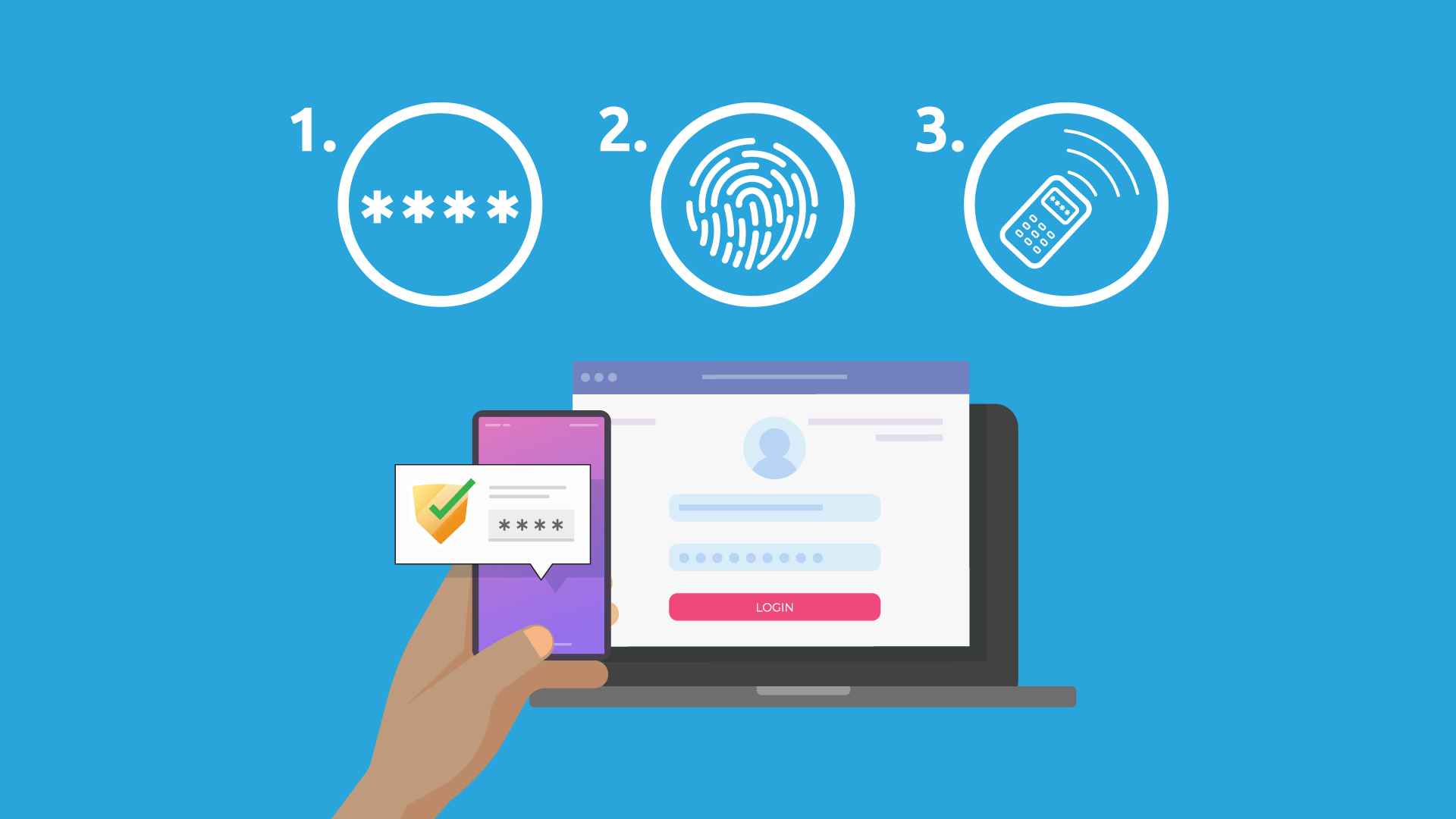
Multi-factor authentication is a security measure that requires users to provide two or more authentication factors to access an application, account, or virtual private network (VPN). This technologically advanced setup secures systems against more sophisticated cyberattacks, preventing credentials from being stolen, exposed, or sold by third parties.
Implementing MFA in your G Network setup is essential for safeguarding against various types of cyber threats. Some of the significant benefits of using MFA include:
- Enhanced Security: MFA adds an extra layer of protection to safeguard systems against unauthorized access and cyber threats by requiring users to provide multiple forms of identity verification.
- Robust Protection: MFA protects against various types of threats, including phishing, spear phishing, and more.
- Improved Compliance: Organizations can comply with regulatory requirements, such as GDPR and HIPAA, by implementing MFA for their security protocols.
- Enhanced User Experience: While MFA can appear to lengthen the login process, it offers a more reliable and trustworthy experience for users.
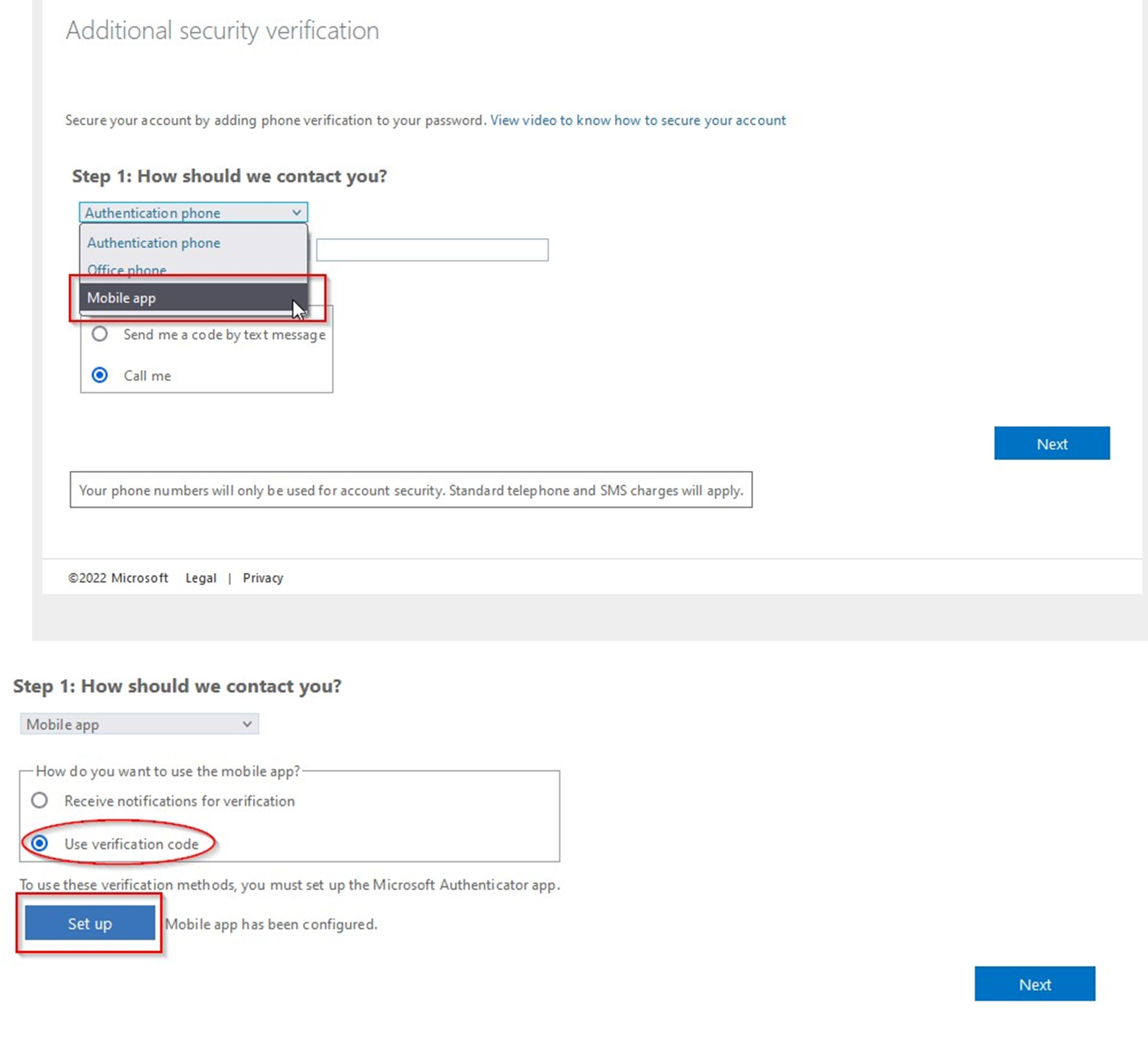
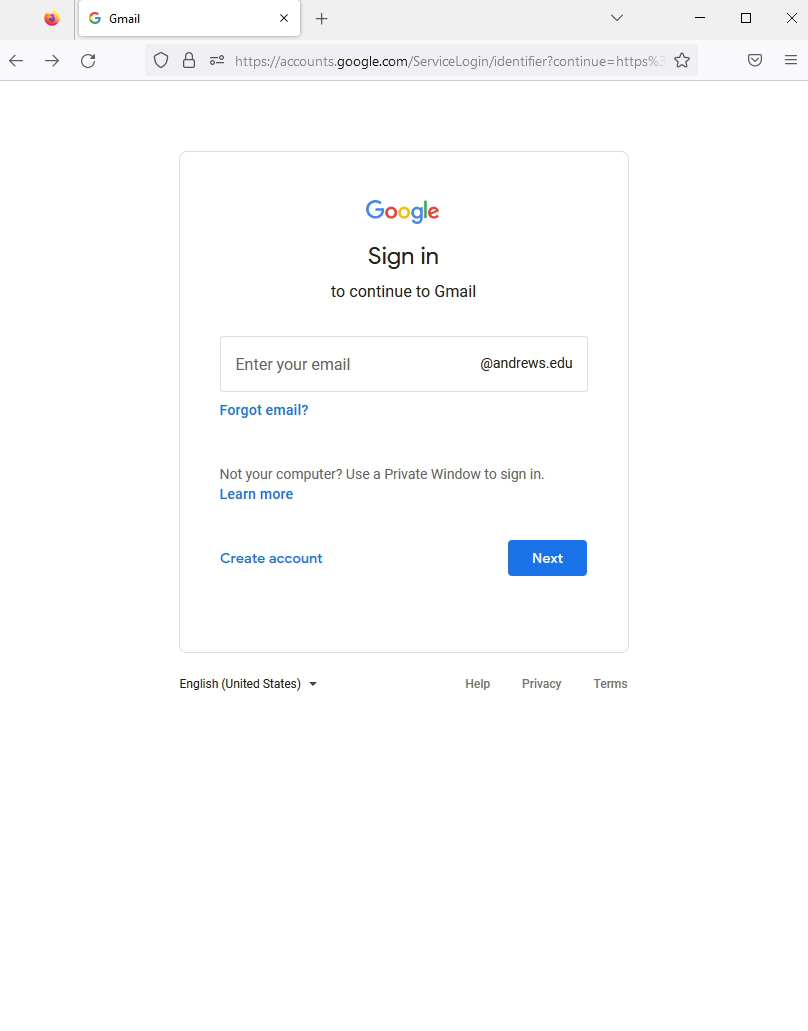
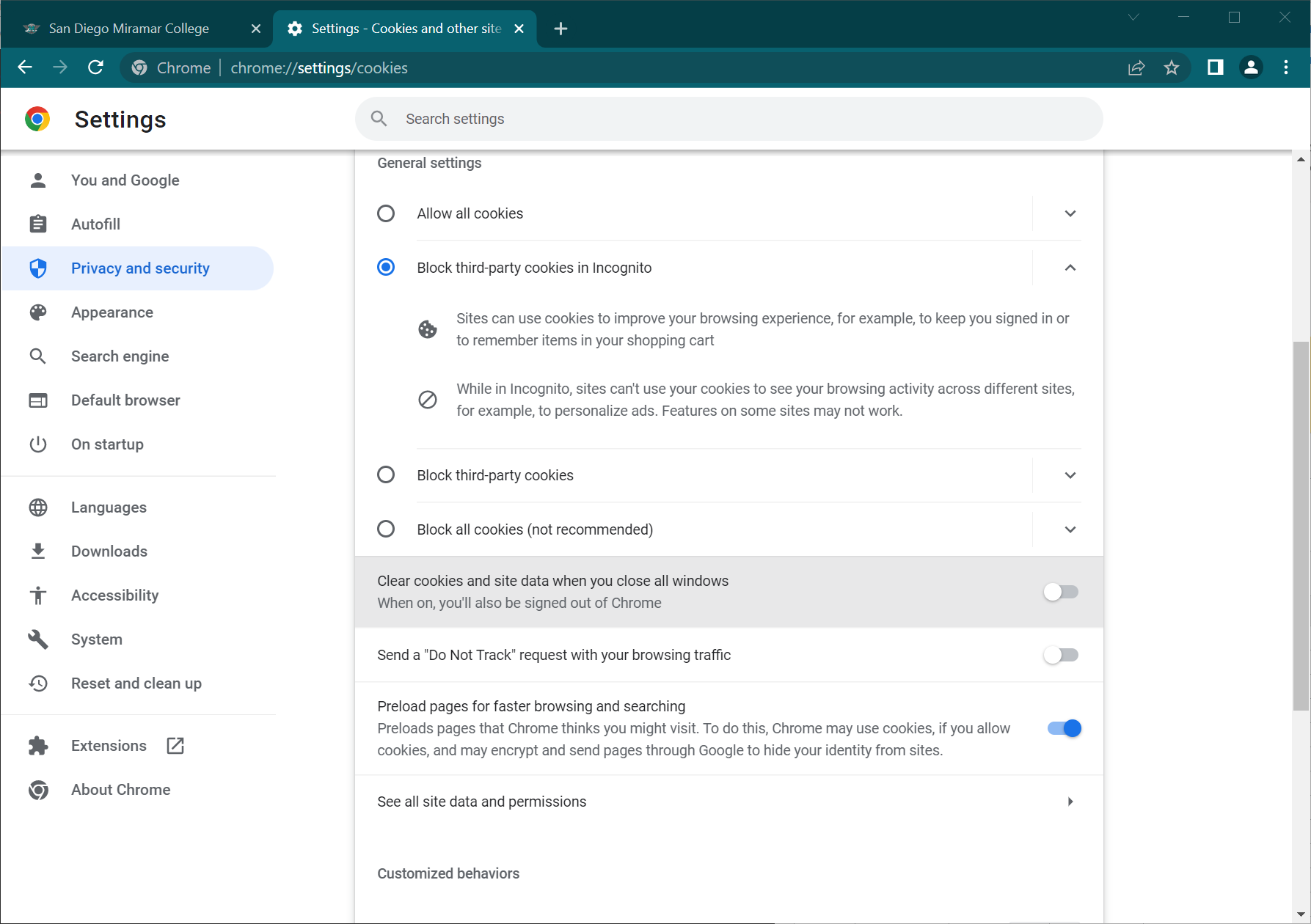
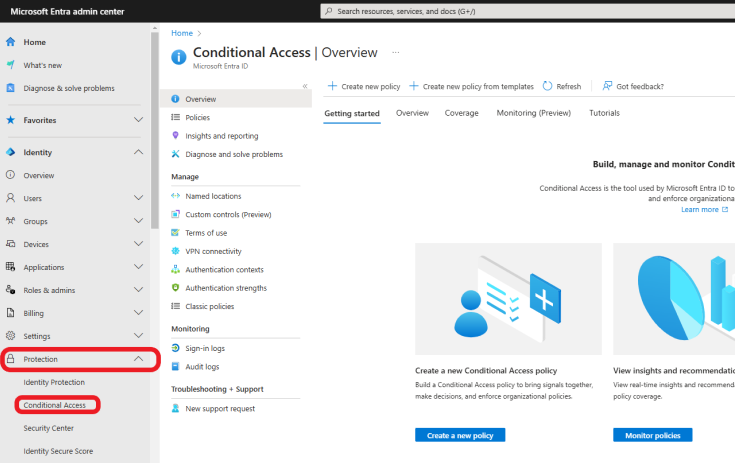
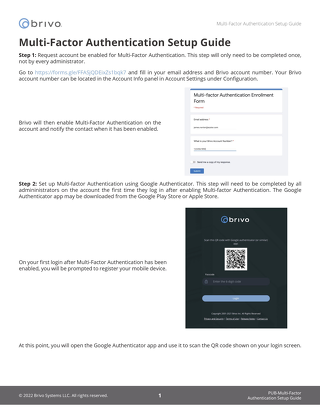
Setting Up G Network for Multi-Factor Authentication

Moving forward, it's essential to keep these visual contexts in mind when discussing G Network Setup For Multi-Factor Authentication.
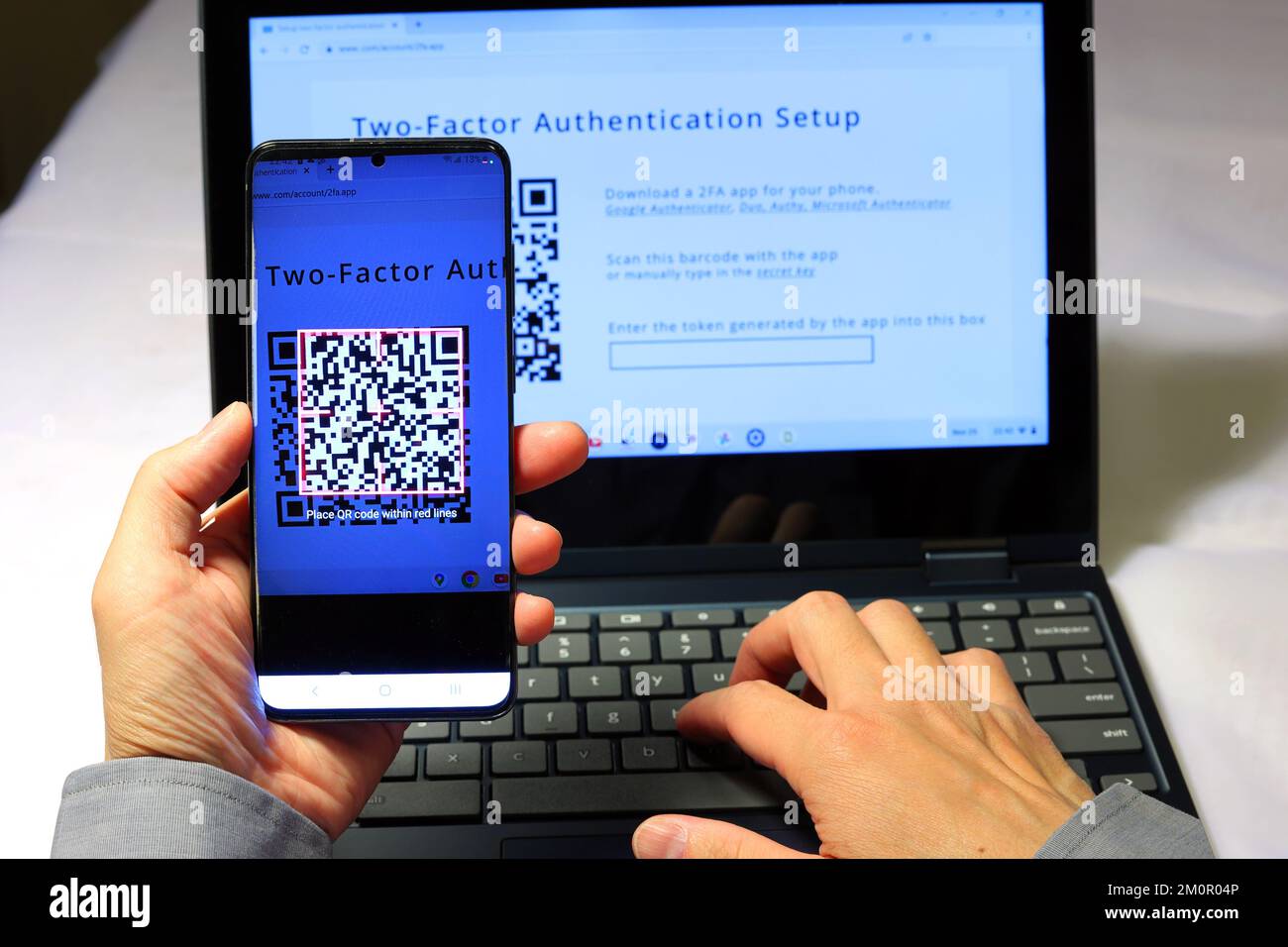
To set up G Network for MFA, follow these steps:
Best Practices for Implementing Multi-Factor Authentication
When implementing MFA in your G Network setup, consider the following best practices to ensure seamless execution:

- Communicate Effectively: Inform users about the importance and use of MFA to minimize user frustration.
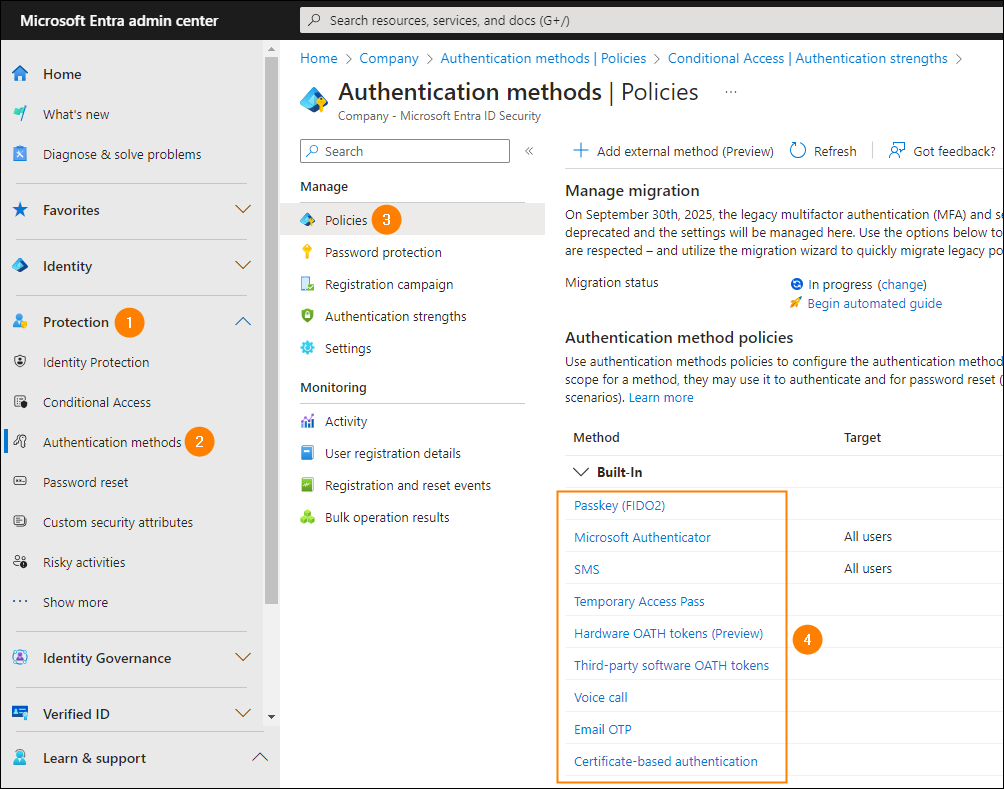
- Choose the Right Solution: Select an MFA solution that fits your organization's needs and budget, from one-time passwords to smart cards and software token applications.
- Analyze Data: Use collected data to optimize the MFA setup, identify weak points, and make necessary adjustments.
Conclusion
Implementing G Network setup for multi-factor authentication offers robust security measures against cyber threats, strengthening your overall network security posture. By selecting the right MFA method, configuring it according to your organization's needs, and following best practices, ensure seamless execution and improve users' trust in the system.