Protecting WiFi Network with Intrusion Detection: A Comprehensive Guide
Introduction

Understanding Wireless Intrusion Detection Systems (WIDS)
The Importance of Intrusion Detection Systems (IDS)




TodayThe rapid growth of Internet of Things (IoT)networkshas increased security risks, making it essential to have effectiveIntrusionDetectionSystems (IDS) for real-time threatdetection.
Sep 12, 2025A stable and secureWiFinetworkis essential for both work and leisure. However, the convenience of wireless connectivity also makes it susceptible to unauthorized access. In this article, we will discuss how to check if yourWiFinetworkis being used by someone else without your permission and provide valuable tips on how to prevent such incidents.

6 days agoGain exclusive access to cybersecurity news, articles, press releases, research, surveys, expert insights and all other things related to information security.

TodayNew fully integratedintrusiondetectionsolution combines best in class performance and wireless technology.

TodayLegacy wired and wirelessintrusionsystems are also somewhat limited in intelligence, lacking the ability to provide real-time insights and system health monitoring with limited reporting for audits and investigations. It's also difficult, if not at all possible, to integrate most legacyintrusiondetectionsystems with modern security and building automation platforms, rendering them as ...
TodayA router with an integrated firewall adds stateful packet inspection,intrusiondetection, and application-level filtering at thenetworkedge, blocking malicious traffic before it reaches any device. According to the 2025 SonicWall Cyber Threat Report, 68% of small business breaches originated fromnetworkperimeter failures.

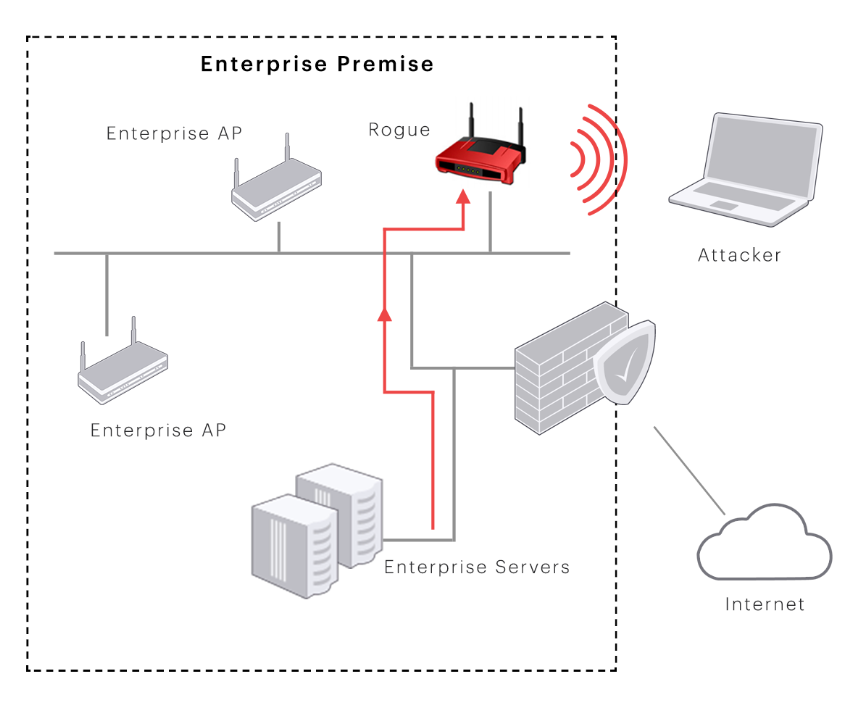
WirelessIntrusionDetectionSystem: Rapidly deployable, encrypted wireless sensors for flexible office spaces or historical buildings where wiring is restricted. Seismic & Pressure Sensors: Specialized protection for vaults, data centers, and critical storage environments. An enterprise-gradeintrusionsystem does more than notify the authorities.

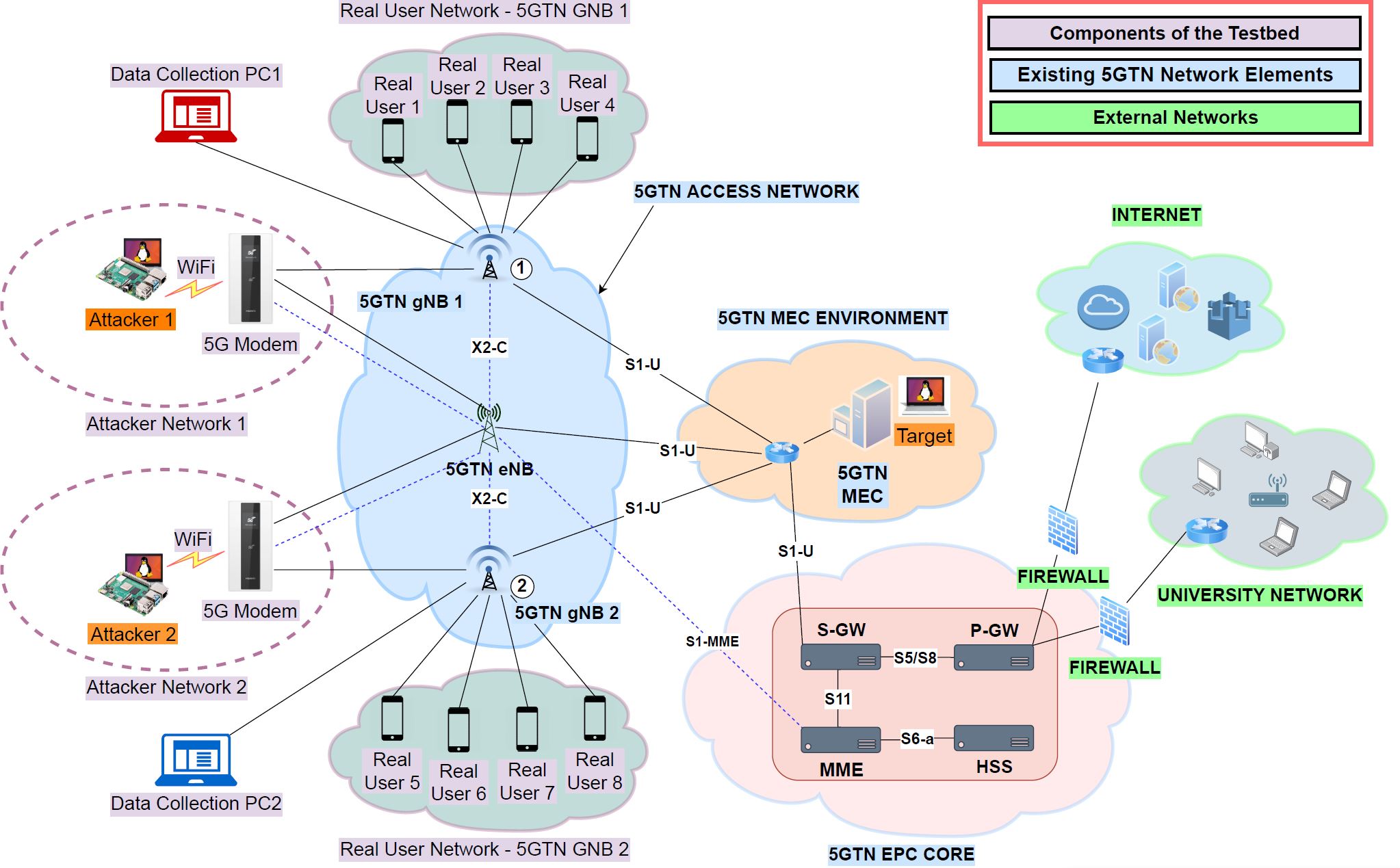
This paper presents anintrusiondetectionsystem utilizing machine learning models, including Random Forest, XGBoost, Decision Tree, and KNN, demonstrating highdetectionperformance and transparency, making it appropriate for real-world applications, includingprotectingoffice and enterpriseWi-Fi, defensenetworks, and improving public Wi ...

2 days agoIntrusiondetectionand prevention systems for optical wirelessnetworks: Security systems can monitor optical wireless communication channels to detect and prevent unauthorized access attempts and malicious activities.
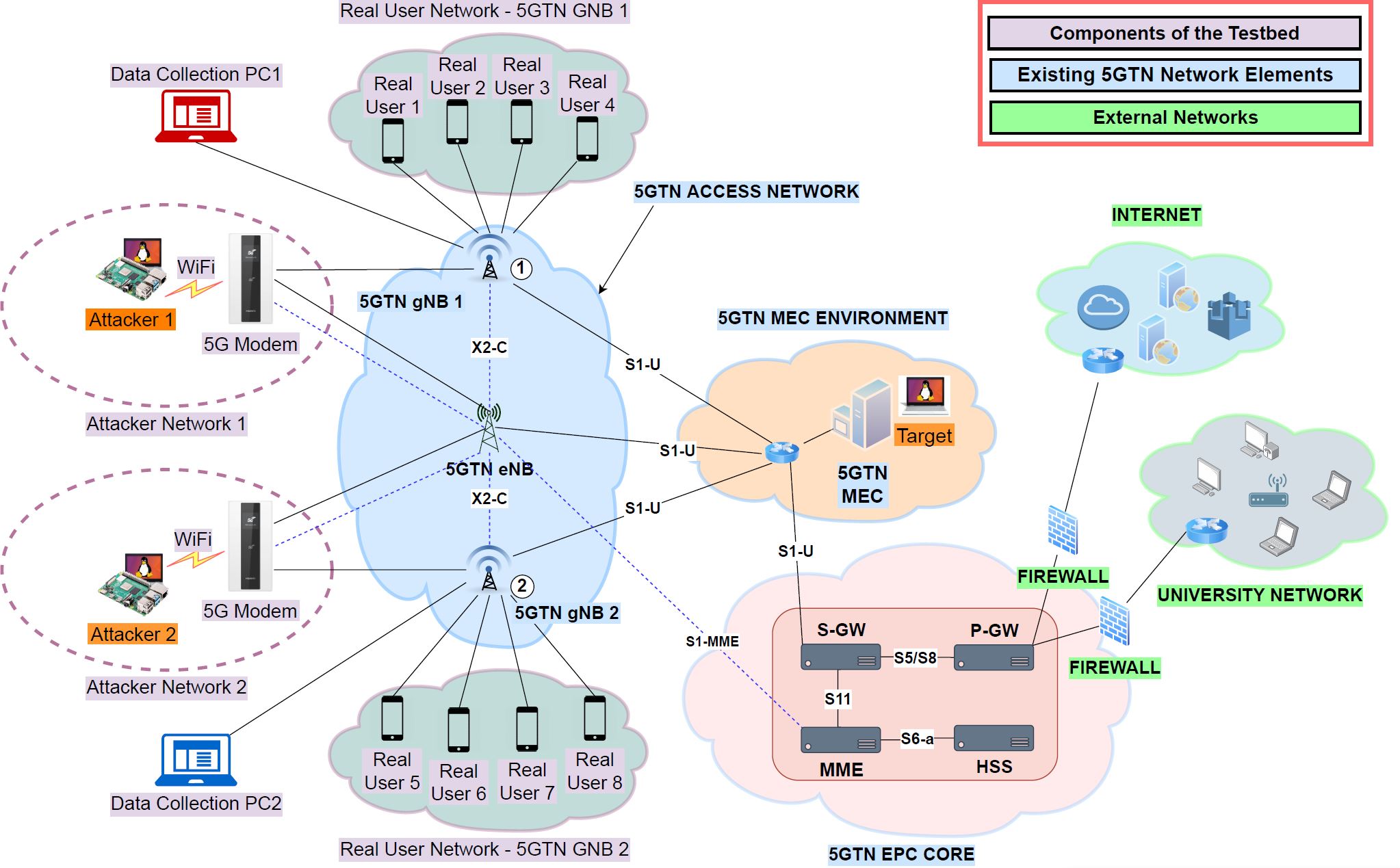
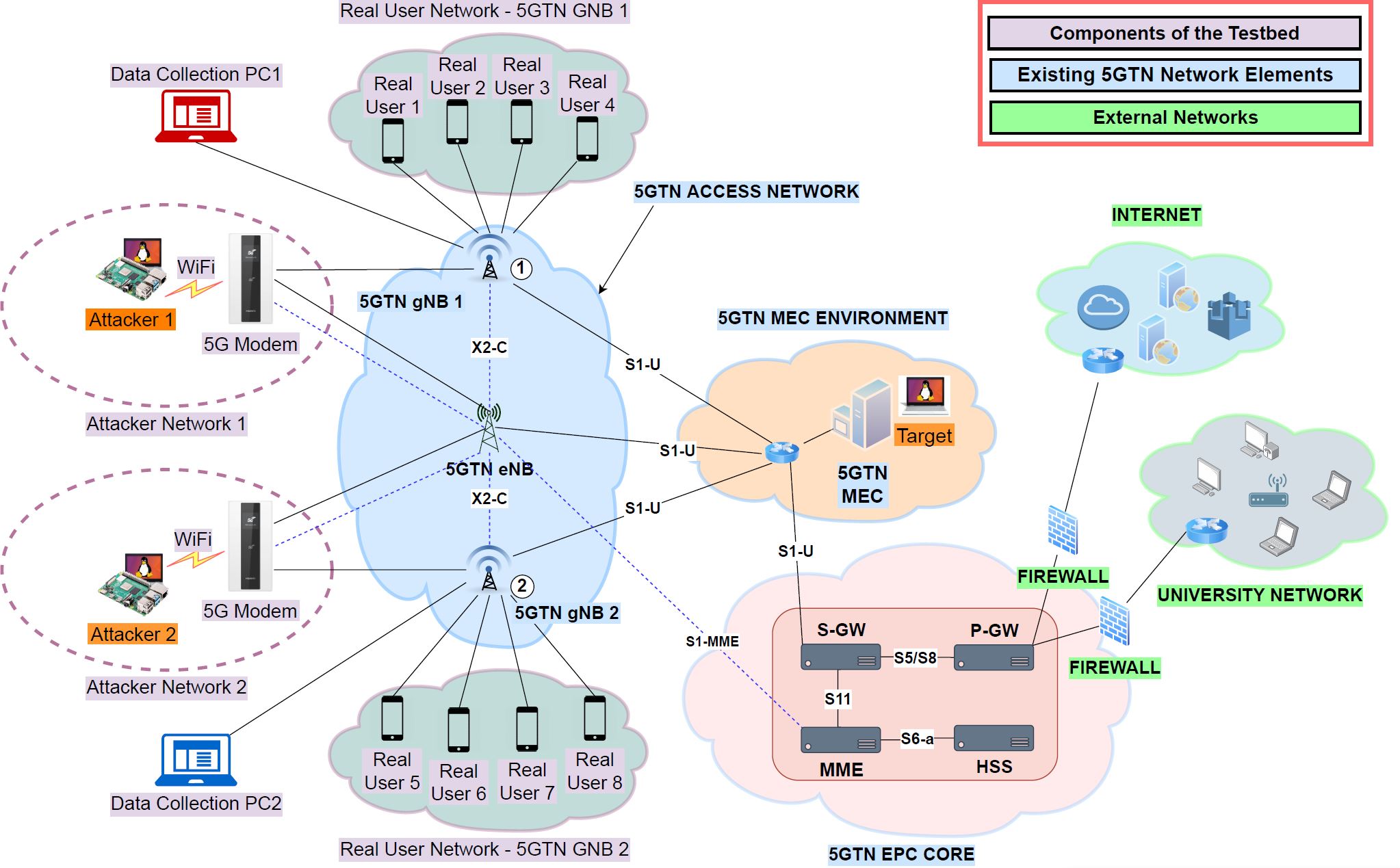
Roguedetection, classification, and mitigation Cisco aWIPS and Rogue Management features roguedetectionand mitigation, as shown in Table 1. Rogue access points and clients can create back-door access to yournetworkand can be used to steal data from your wireless clients.
Sep 15, 2025Wireless security is critically important forprotectingwirelessnetworksand services from unwanted attacks. Here's a quick guide to follow.
Find the best home security with top alarm systems from ADT, a trusted security company with 150 years of experience. Get a good house security system customized for your needs.

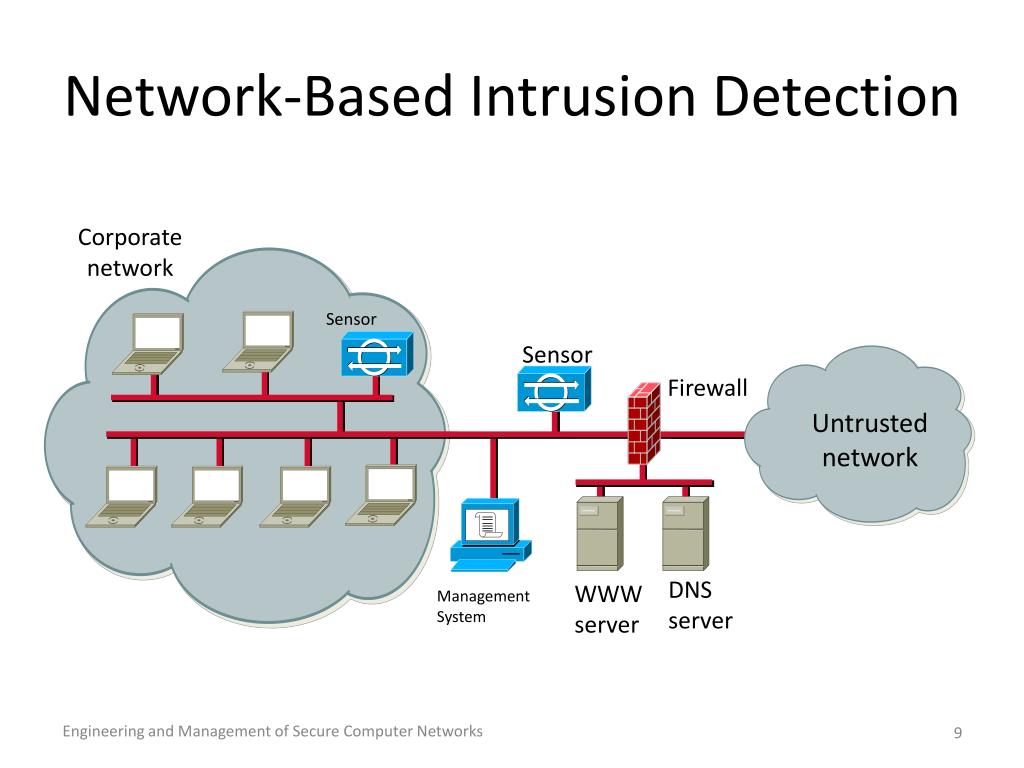
Here are some of the most importantnetworksecurity devices: Firewall - First line of defense against unauthorized access Antivirus - Detects and removes malicious software IDS (Intrusion...

When combined with AI-based security mechanisms like encryption andintrusiondetection, it improves human-centric applications such as health services, military operations, and environmental monitoring. Suchnetworksare weak due to resource constraints and the openness of wireless communication.

Protect your business with expertnetworksecurity services in Lewisville, Texas. Custom Information Services provides firewall management,intrusiondetection,networkmonitoring, VPN setup, and advanced threat protection to secure yournetworkinfrastructure and prevent cyber attacks in Lewisville and nearby areas.

24. NetworkDefender NetworkDefender is a powerfulWiFisecurity tool that focuses on proactivenetworkdefense. It employs advancedintrusiondetectionand prevention techniques to identify and block potential threats in real time.
![Wi-Fi security: How to protect your wireless network [2026 guide] Image showcasing Wi-Fi security: How to protect your wireless network [2026 guide]](http://bastille.net/wp-content/uploads/bastille-networks-comprehensive-wireless-intrusion-detection-system.png)
Nov 24, 2025Learn how to protect your wirelessnetworkwithmodernWi-Fisecurity, WPA3, 802.1X, and Zero Trust. Explore threats, authentication methods, and best practices.
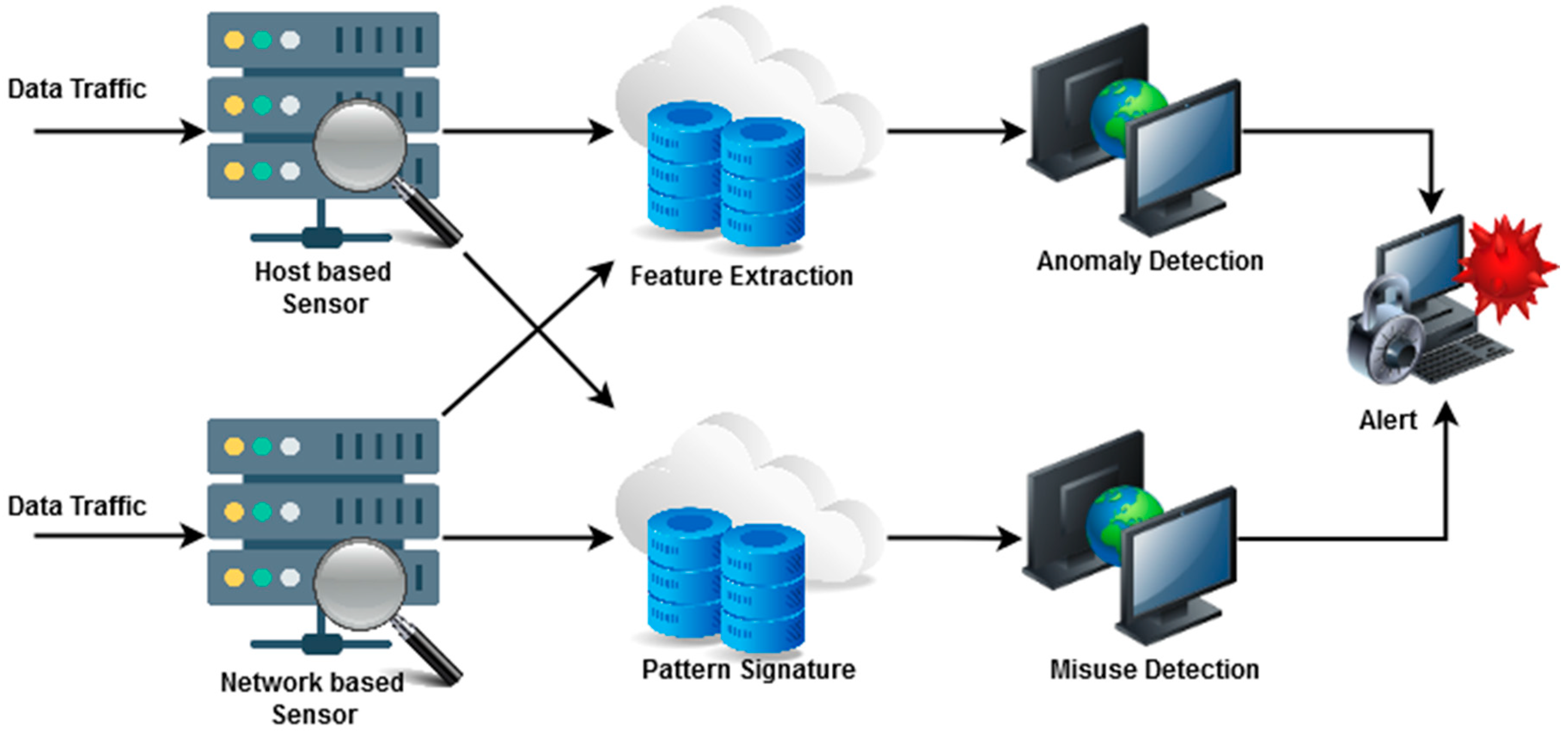
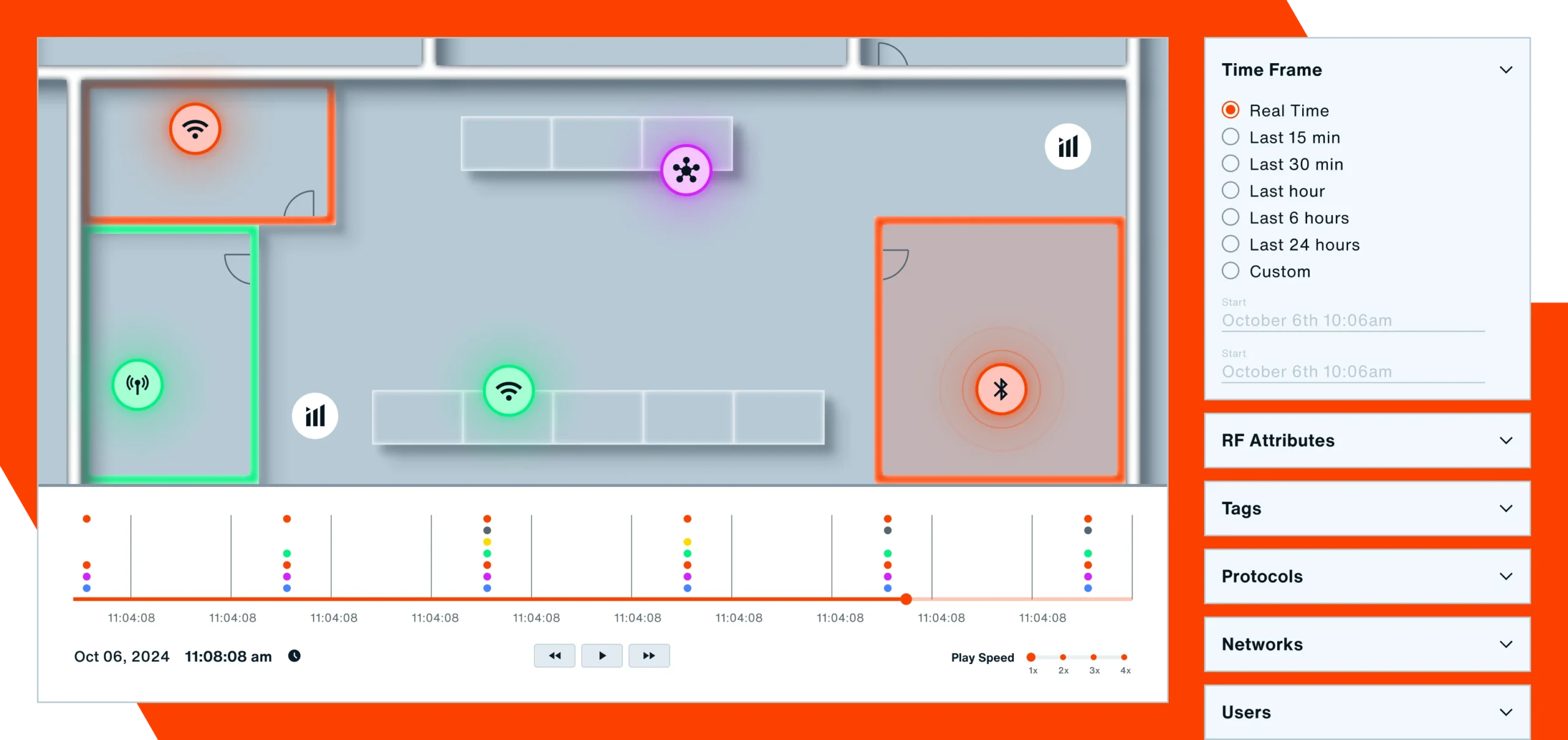
WIDS stands for wirelessintrusiondetectionsystem. It is a technology designed to protect wirelessnetworksfrom unauthorized access. It does this by monitoring traffic on thenetworkto identify any suspicious activity that may indicate a security breach. WIPS stands for wirelessintrusionprevention system. WIPS uses a combination of techniques to detect and preventintrusionsin real time ...
In today's digital age, a stable and secureWiFinetworkis essential for both work and leisure. However, the convenience of wireless connectivity also makes it susceptible to unauthorized ...
Sep 8, 2025Given the unique risks associated with wireless infrastructure, businesses needintrusionprevention tools specifically designed to monitor and defend thesenetworks. WIDS offer this critical layer of protection by scanning thesenetworksfor issues such as unauthorized activity, suspicious access points, spoofed devices and policy violations. Unlike wiredintrusiondetectionand prevention ...

Anintrusiondetectionsystem (IDS) is a device or software application that monitors anetworkor systems for malicious activity or policy violations. [1] Anyintrusionactivity or violation is typically either reported to an administrator or collected centrally using a security information and event management (SIEM) system.

Safe GuestWiFiUse:ProtectingYour Business and Your Visitors Offering guestWiFiis a convenience customers and partners expect but without proper safeguards, it can create significant security ...

Leverage educational content like blogs, articles, videos, courses, reports and more, crafted by IBM experts, on emerging security and identity technologies.

Bastille WirelessIntrusionDetectionmonitors RF activity, finds rogue devices, and alerts you to wireless security threats fast.

This paper presents anintrusiondetectionsystem utilizing machine learning models, including Random Forest, XGBoost, Decision Tree, and KNN, demonstrating highdetectionperformance and transparency, making it appropriate for real-world applications, includingprotectingoffice and enterpriseWi-Fi, defensenetworks, and improving public Wi ...

Snort is an open-source, free and lightweightnetworkintrusiondetectionsystem (NIDS) software for Linux and Windows to detect emerging threats.

1 day ago03Intrusiondetectionand threat monitoring systems Connected exoskeleton systems benefit from integratedintrusiondetectionand threat monitoring capabilities that continuously analyze system behavior andnetworktraffic for suspicious activities. These systems employ machine learning algorithms and anomalydetectiontechniques to identify potential cybersecurity threats in real-time. When ...

May 14, 2025Protect enterpriseWi-Fiwitha wirelessintrusiondetectionsystem that monitors threats, flags rogue devices, and strengthensnetworkvisibility.
IntrusionDetectionSystem Works On Which Layer It is the responsibility of the wirelessintrusiondetectionsystem (WIDS) to Layer 2 attacks involve manipulating management and control frames used to testing security for vulnerabilities, clients would operate under a false belief that their. It is an intelligent system which is deployed on the physical layer in anetworkwhich then ids. Here ...