Anticipating Phishing Attempts with the Right Software
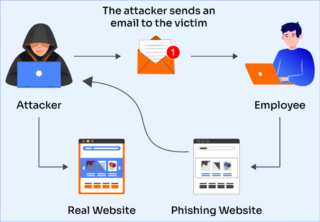
In today's digital landscape, individuals and organizations are constantly at risk of falling victim to cleverly crafted phishing scams. The ease with which attackers can masquerade as trusted sources, combined with the unsuspecting nature of targets, makes phishing a persistent threat. However, anticipating phishing attempts with the right software can significantly mitigate this risk.What is Phishing Software?
Phishing software is a cybersecurity tool designed to detect and block phishing attempts in real-time. It uses sophisticated algorithms to analyze email content and URLs, identifying suspicious behavior indicative of phishing attacks. These tools can not only flag malicious messages but also educate users on how to avoid falling prey to these common cyber threats.Features to Look for in Phishing Software

As we can see from the illustration, Anticipating Phishing Attempts Software has many fascinating aspects to explore.
When selecting an anti-phishing software, several essential features should be at the top of your list:- Real-time threat analysis: The software should be able to analyze emails and URLs in real-time, providing immediate protection against new threats.
- Machine learning algorithms: Machine learning-based algorithms can identify patterns associated with phishing attempts, making the software more effective over time.
- Customization: The ability to create custom phishing templates and scenarios will help you simulate real-world threats, ensuring your team is prepared for any scenario.
- Integration:** Choosing a solution that integrates seamlessly with your existing email systems will make training and protection easier to manage.
- Reporting and analytics: The ability to track and analyze campaign metrics is crucial for adjusting your anti-phishing training and identifying areas for improvement.
- Comprehensive threat protection:** Look for software that not only identifies phishing emails but also protects against other types of cyber threats.
Best Practices for Implementing Phishing Software

- Regular updates and maintenance:** Stay up to date with the latest security patches and software updates to ensure the latest threats are covered.
- Customize training: Tailor your training to your team's specific needs and concerns, keeping scenarios fresh and relevant.
- Range comprehensive infrastructure protection:** Combine anti-phishing software with other security measures to guarantee a solid defense against the complete spectrum of cyber threats.




![7 Best Anti-Phishing Software Solutions for 2025 [AI-Powered Security] 7 Best Anti-Phishing Software Solutions for 2025 [AI-Powered Security]](https://www.itarian.com/blog/wp-content/uploads/2025/06/vishing.png)



-1.webp)