G Network Security Setup for IT Infrastructure
The foundation of security, availability, and performance for any IT infrastructure is proper network configuration. Network segmentation is a critical aspect of this, significantly reducing the ability for an adversary to reach and exploit other systems. In this article, we will explore a G network security setup for IT infrastructure, highlighting the importance of network security and providing a step-by-step guide to implementing a robust security measure.
Understanding Network Security Infrastructure
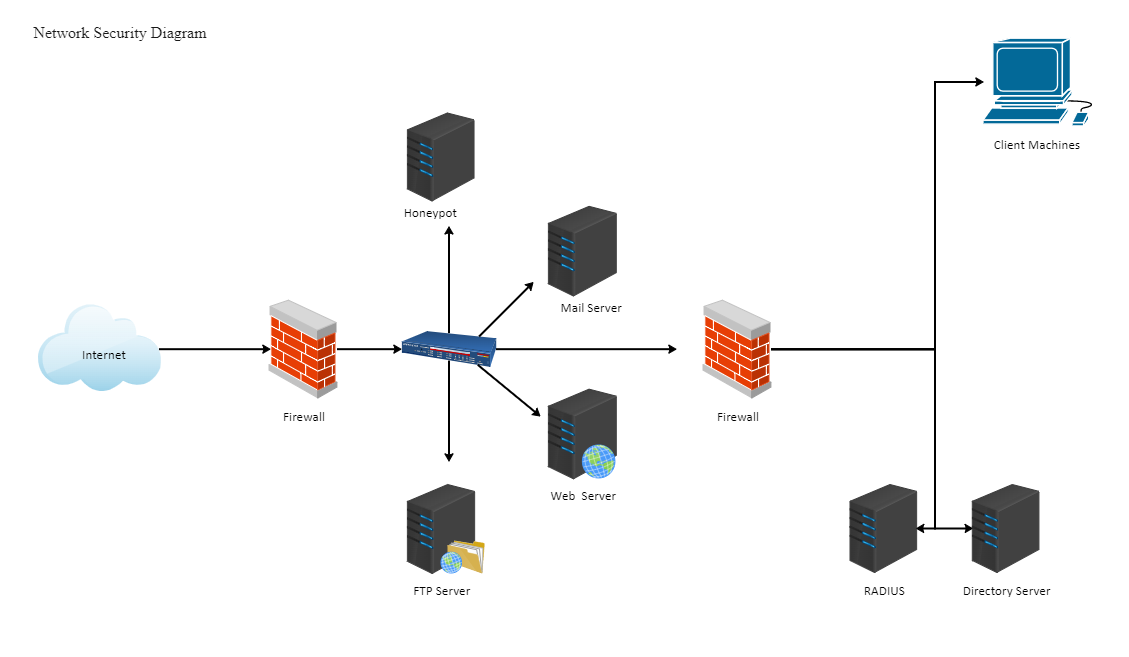
Key Components of Network Security Infrastructure
- Firewalls: Prevent unauthorized access to network resources
- Intrusion Detection and Prevention Systems: Detect and prevent malicious activity on the network
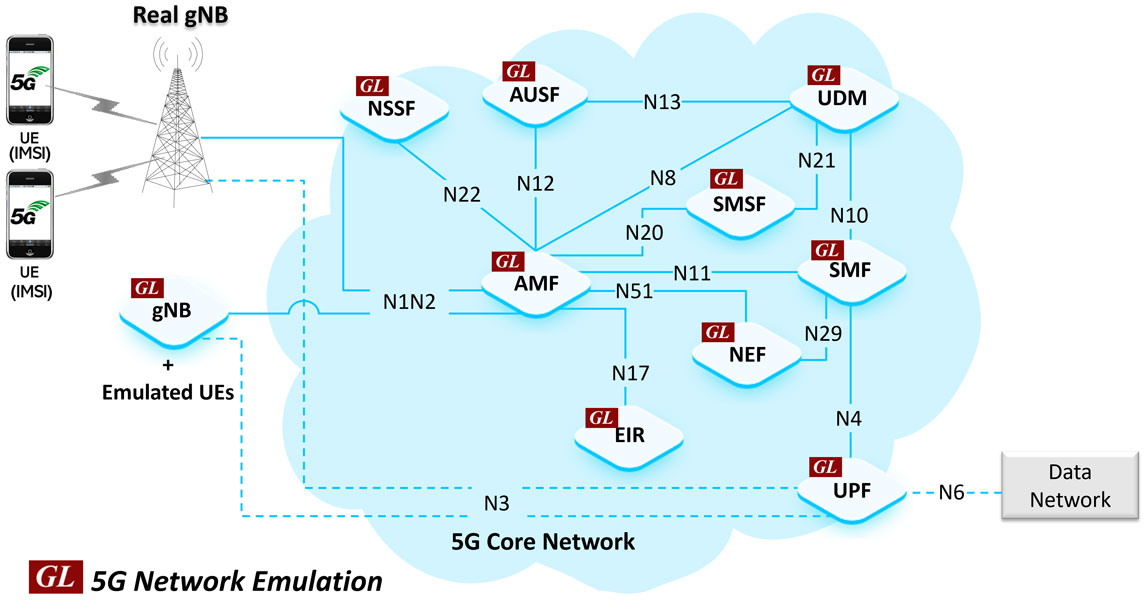
- Virtual Private Networks (VPNs): Encrypt network traffic and provide secure access to network resources
- Access Control Systems: Manage who has access to network resources and what they can do with them
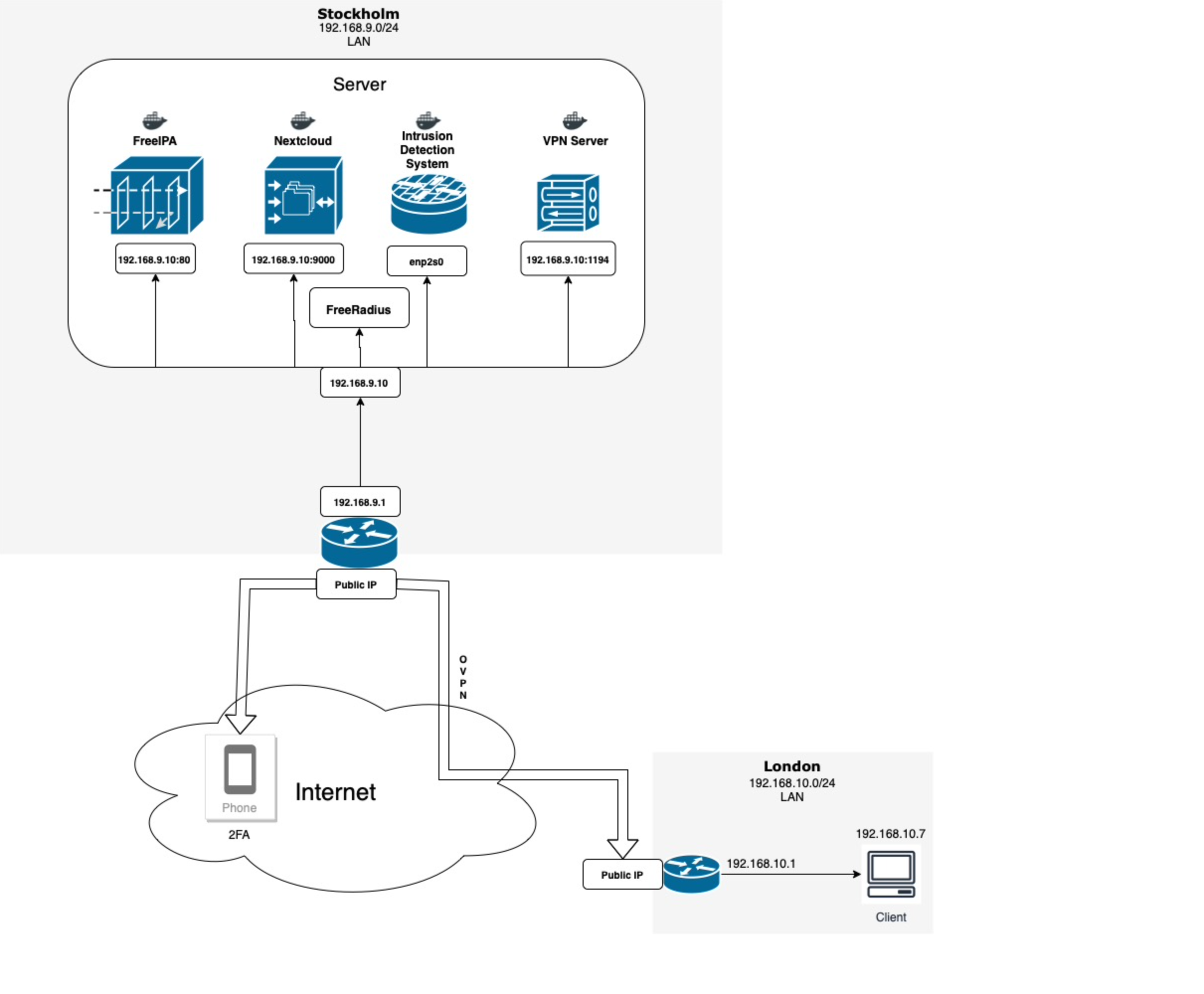
Implementing G Network Security Setup for IT Infrastructure
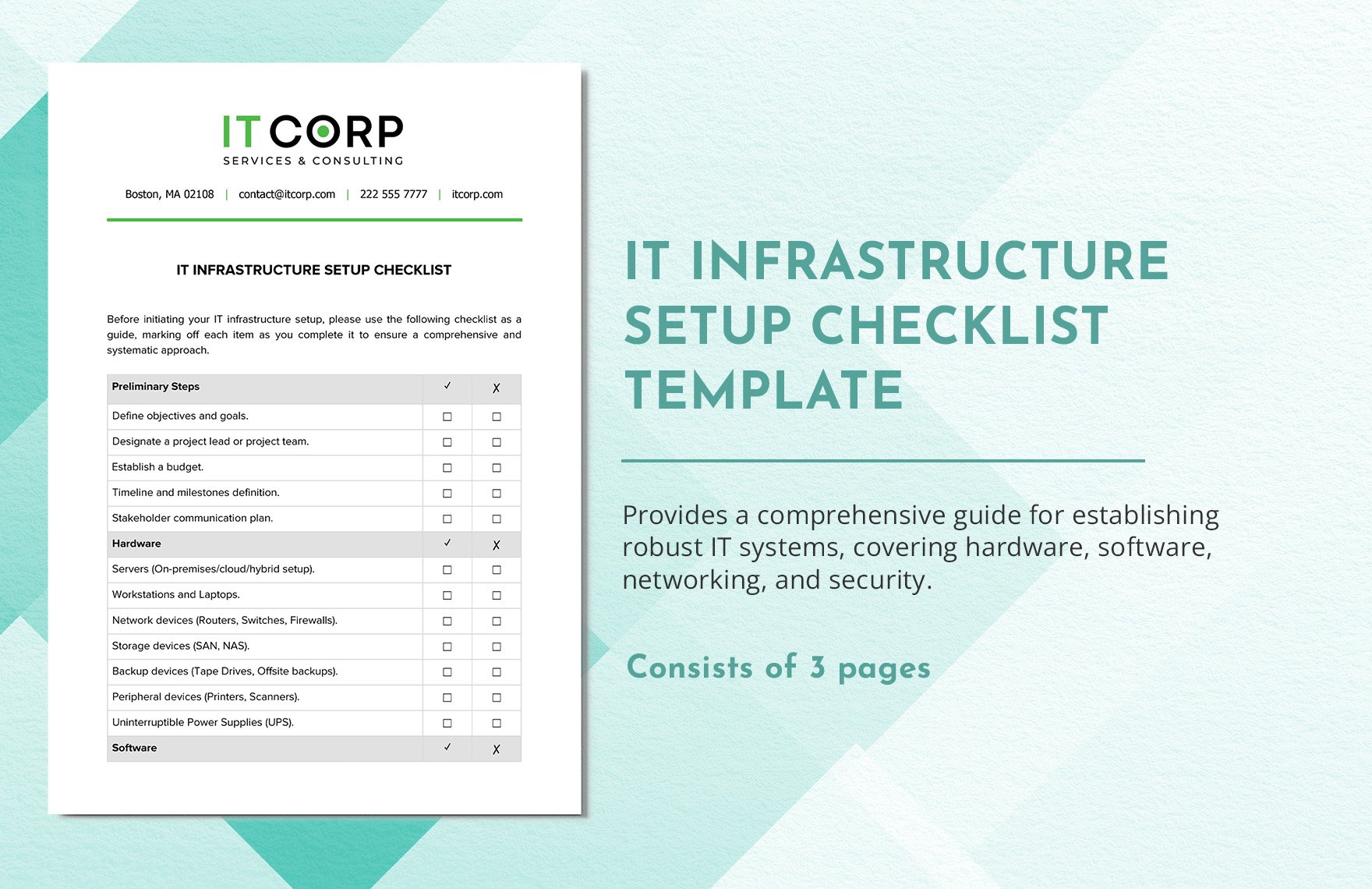
Implementing a G network security setup for IT infrastructure involves several critical steps. These include:
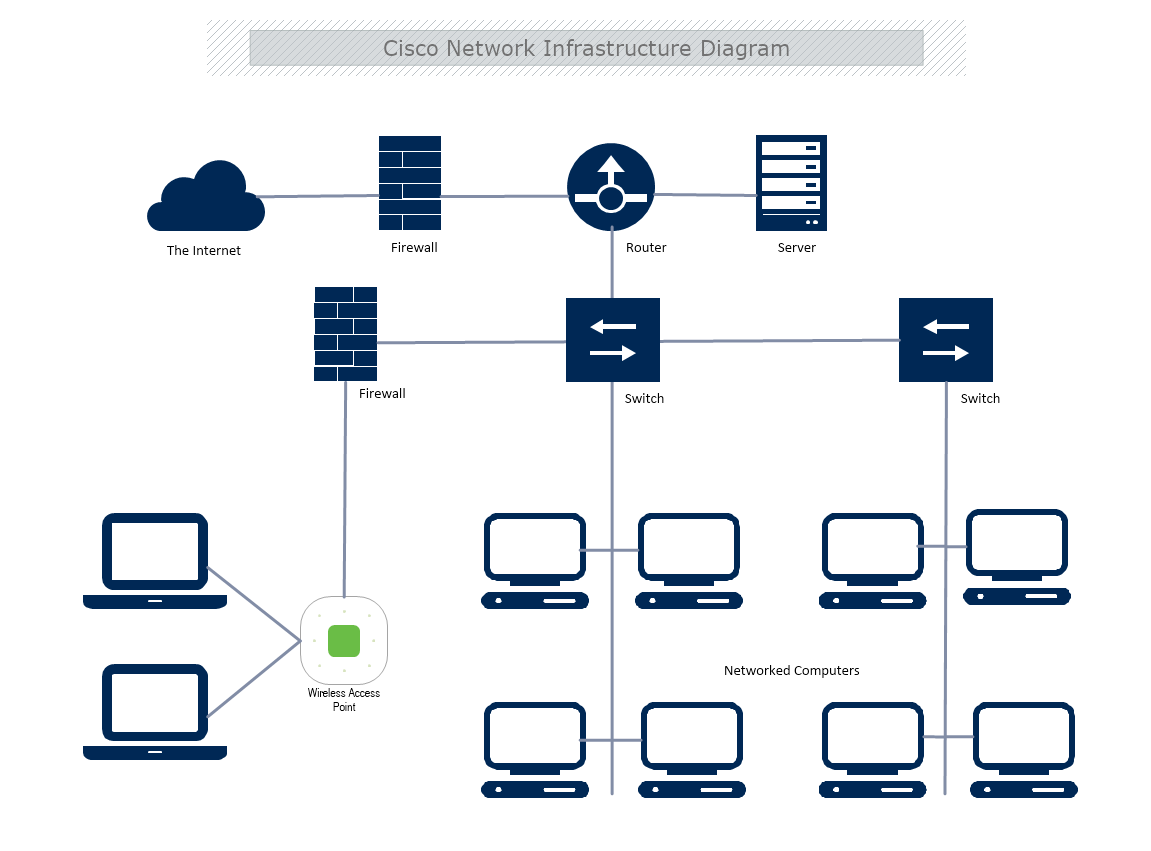
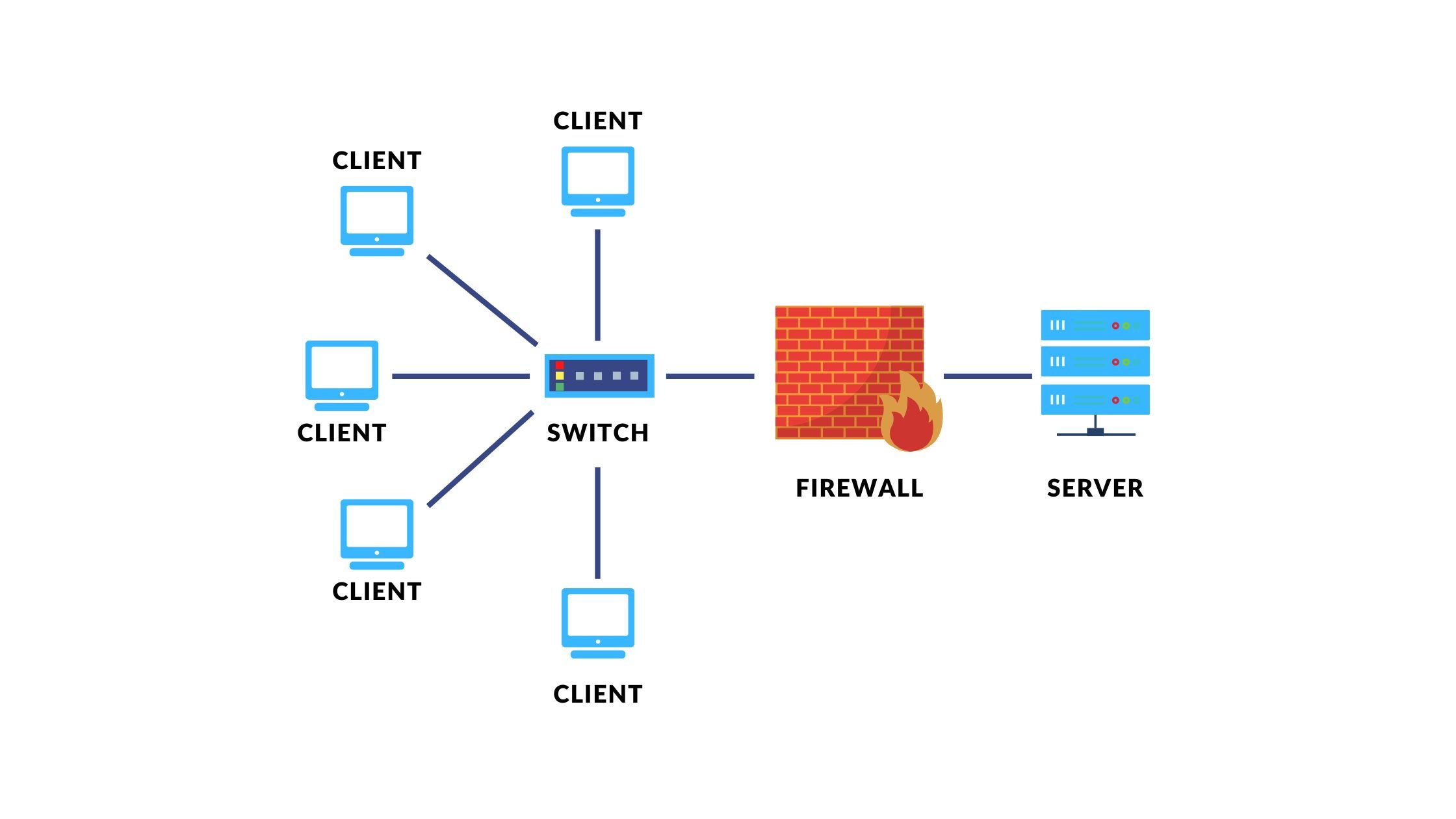
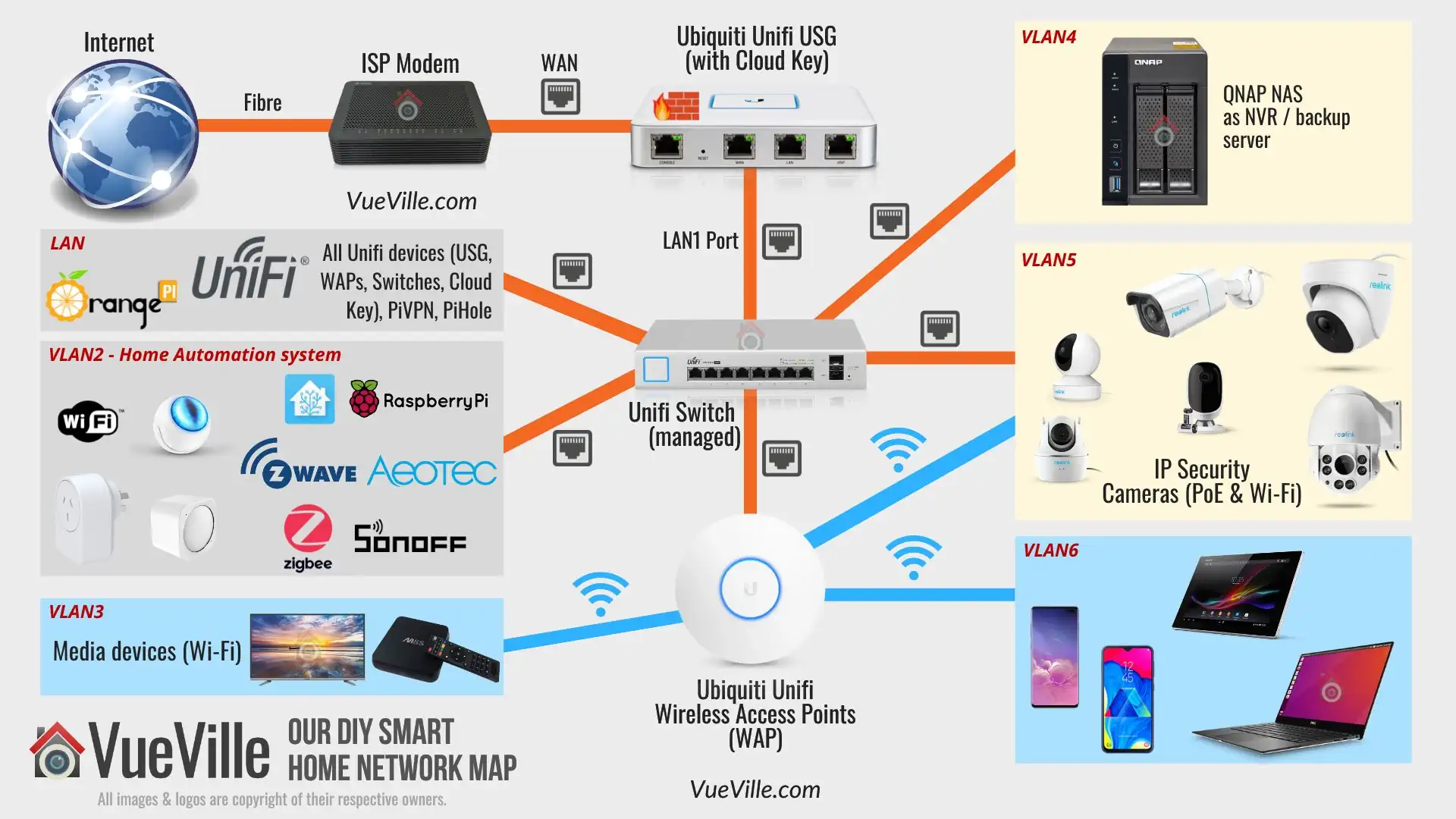
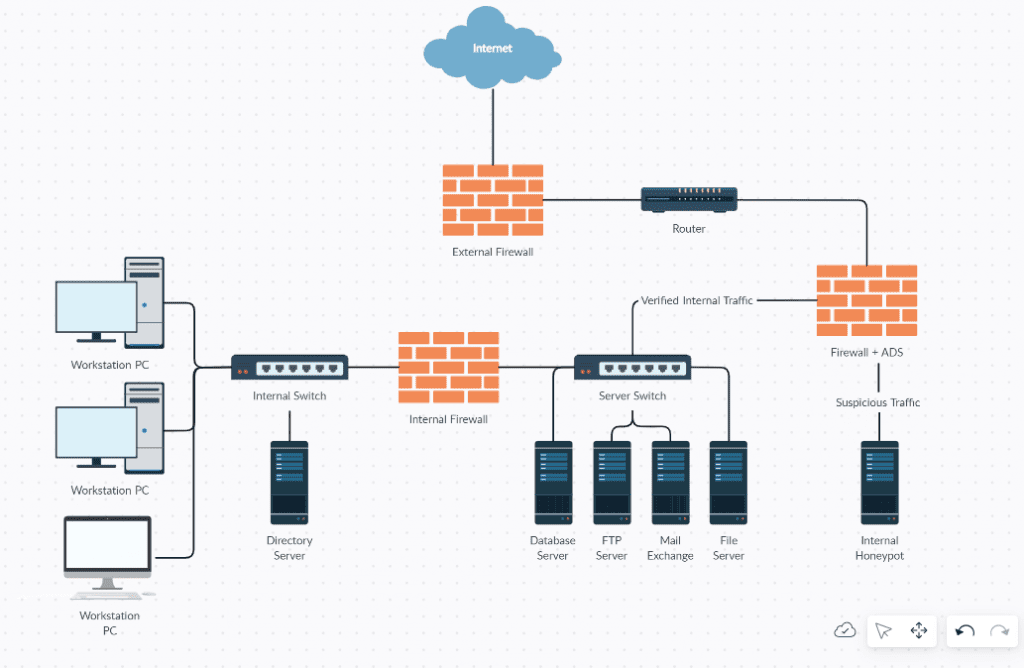
Step 1: Network Segmentation
Network segmentation is a critical aspect of network security. It involves dividing the network into smaller sub-networks, each with its own access controls and security measures. This makes it more difficult for an adversary to move laterally across the network and exploit other systems.
Step 2: Implementing Firewalls
Firewalls are a critical component of network security. They prevent unauthorized access to network resources and filter out malicious traffic. Firewalls should be configured to allow only necessary traffic and block all other traffic.

Such details provide a deeper understanding and appreciation for G Network Security Setup For It Infrastructure.
Step 3: Implementing Intrusion Detection and Prevention Systems
Intrusion detection and prevention systems (IDPS) detect and prevent malicious activity on the network. They can identify and block known and unknown threats, providing an additional layer of security.
Step 4: Implementing Virtual Private Networks (VPNs)
Step 5: Implementing Access Control Systems
Access control systems manage who has access to network resources and what they can do with them. They provide the necessary level of access based on user roles and responsibilities.

Benefits of G Network Security Setup for IT Infrastructure
A well-implemented G network security setup for IT infrastructure provides several benefits, including:
- Reduced risk of cyber attacks and data breaches
- Improved network security and confidentiality
- Enhanced compliance with regulatory requirements
- Increased productivity and reduced downtime
Conclusion
In conclusion, a G network security setup for IT infrastructure is a critical component of any organization's overall security strategy. By implementing a robust security measure, organizations can reduce the risk of cyber attacks and data breaches, improve network security and confidentiality, and enhance compliance with regulatory requirements. By following the steps outlined in this article, organizations can implement a G network security setup that meets their specific needs and provides the necessary level of security and protection.