G Router Denial of Service (DoS) Protection Setup: A Comprehensive Guide
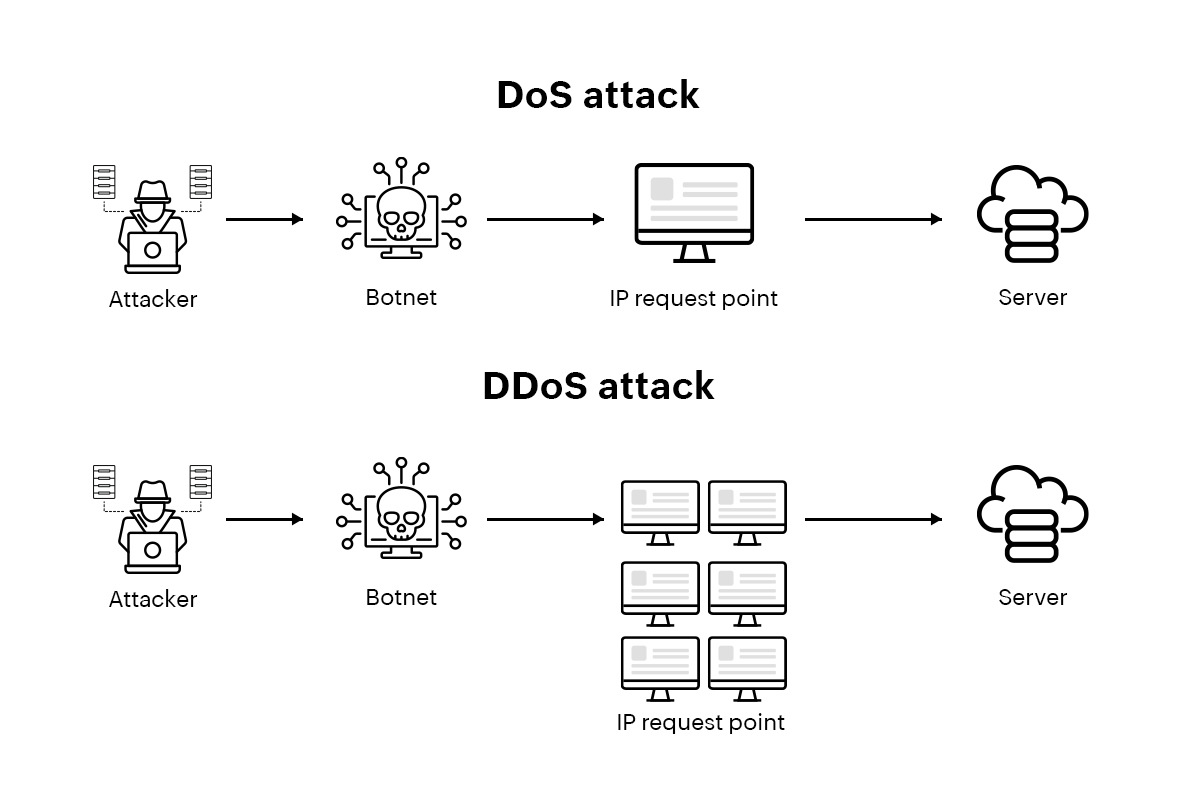
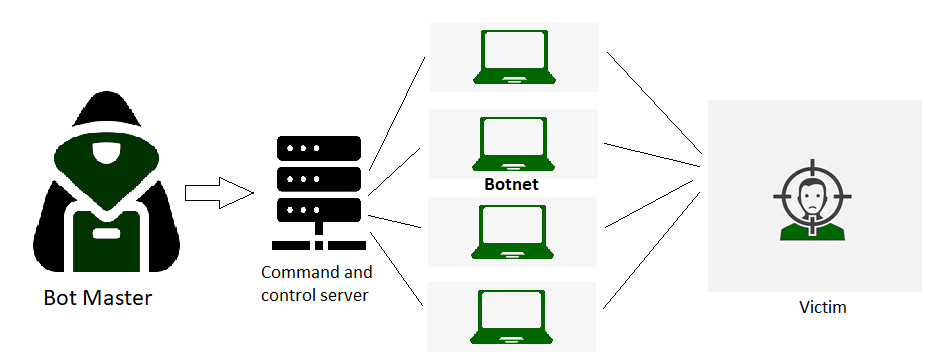
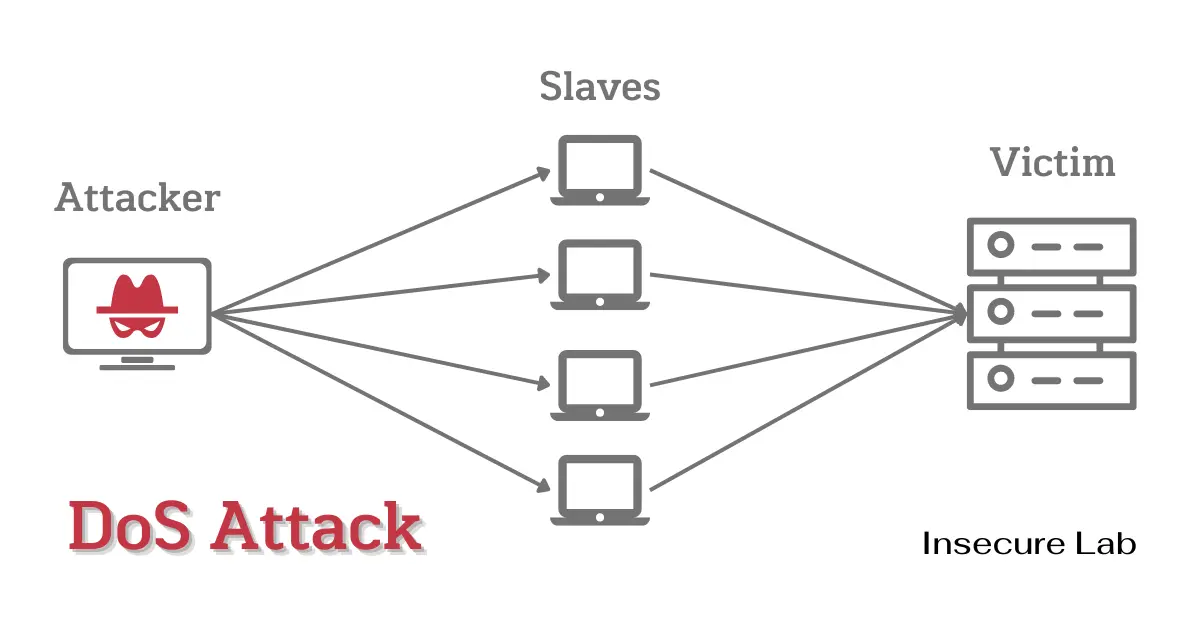
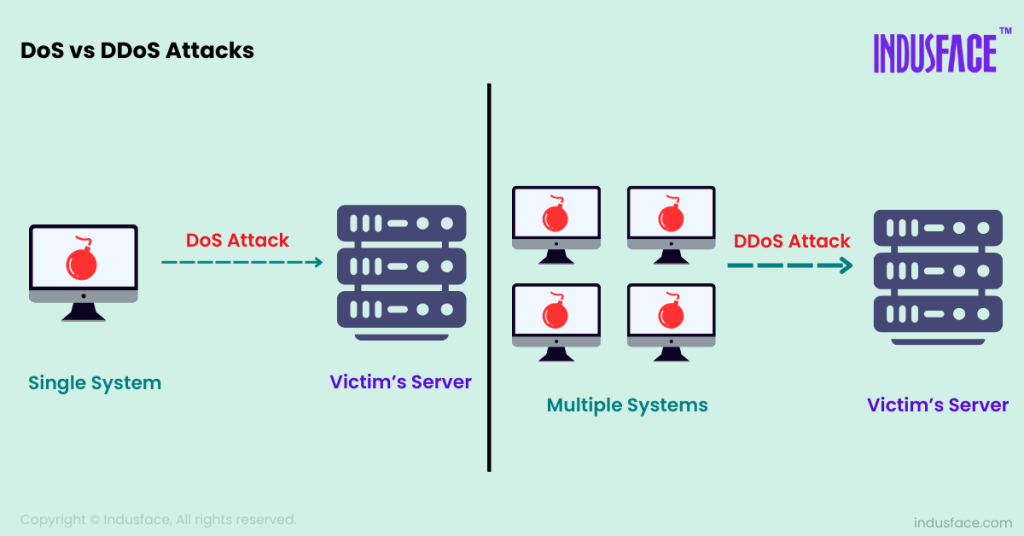
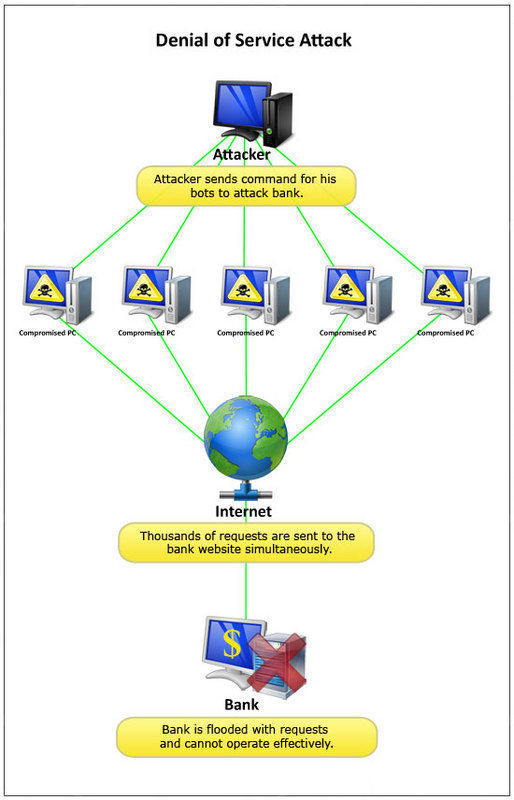
A DoS attack is a type of cyber attack where an attacker intentionally floods a network with traffic in order to render it unavailable to legitimate users. This can be done in a variety of ways, including by sending a large amount of traffic to a single server or by flooding the network with traffic from multiple sources.
DoS attacks can be particularly damaging to businesses and organizations because they can bring online services to a grinding halt, resulting in lost revenue and damage to reputation. In order to protect against DoS attacks, it is essential to have a comprehensive security setup in place, including a G Router Denial of Service (DoS) Protection Setup.
The Importance of G Router Denial of Service (DoS) Protection Setup
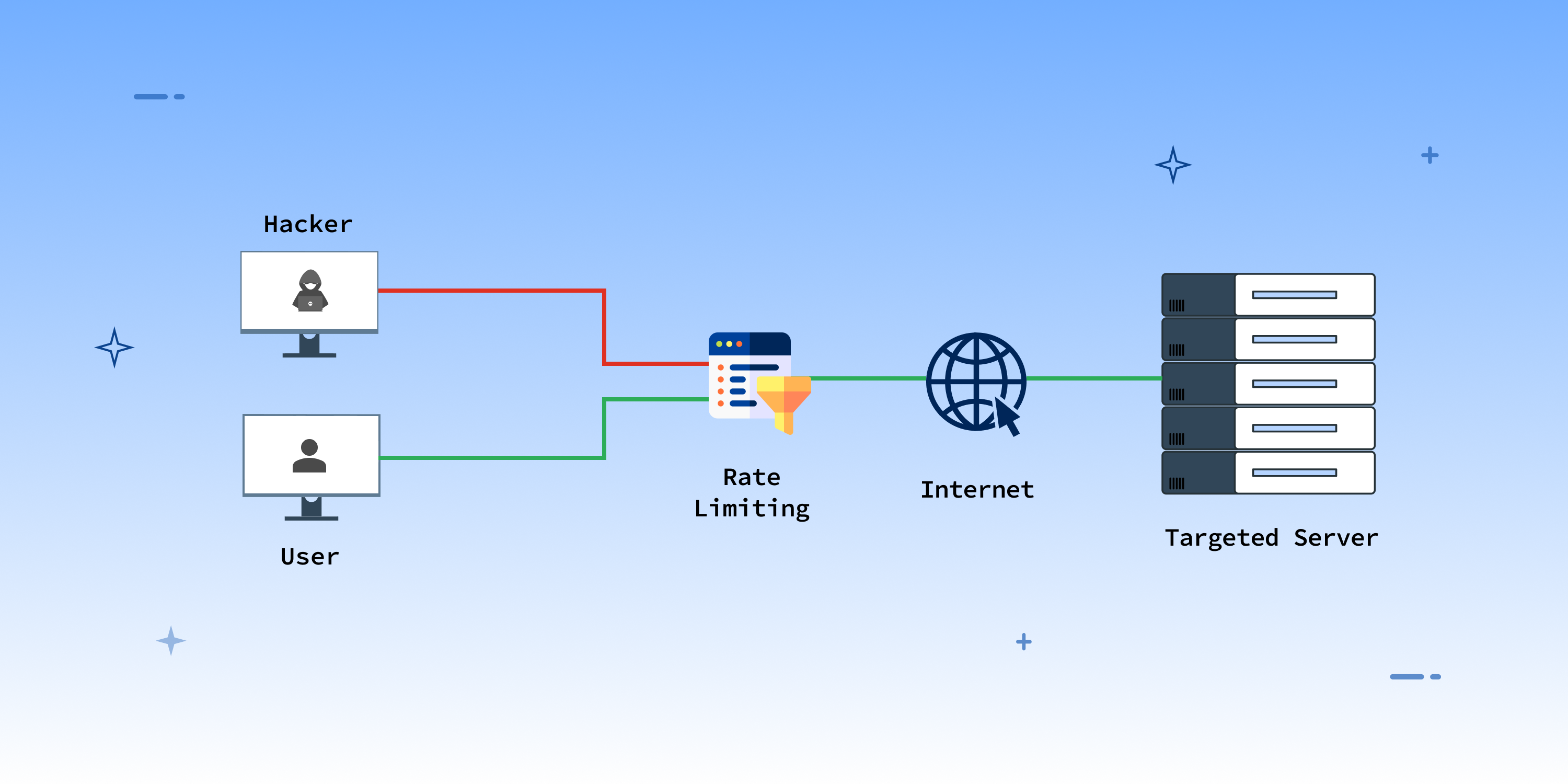
A G Router Denial of Service (DoS) Protection Setup is a critical component of a comprehensive network security setup. It helps to prevent DoS attacks by filtering out malicious traffic and ensuring that only legitimate traffic is allowed to enter the network.
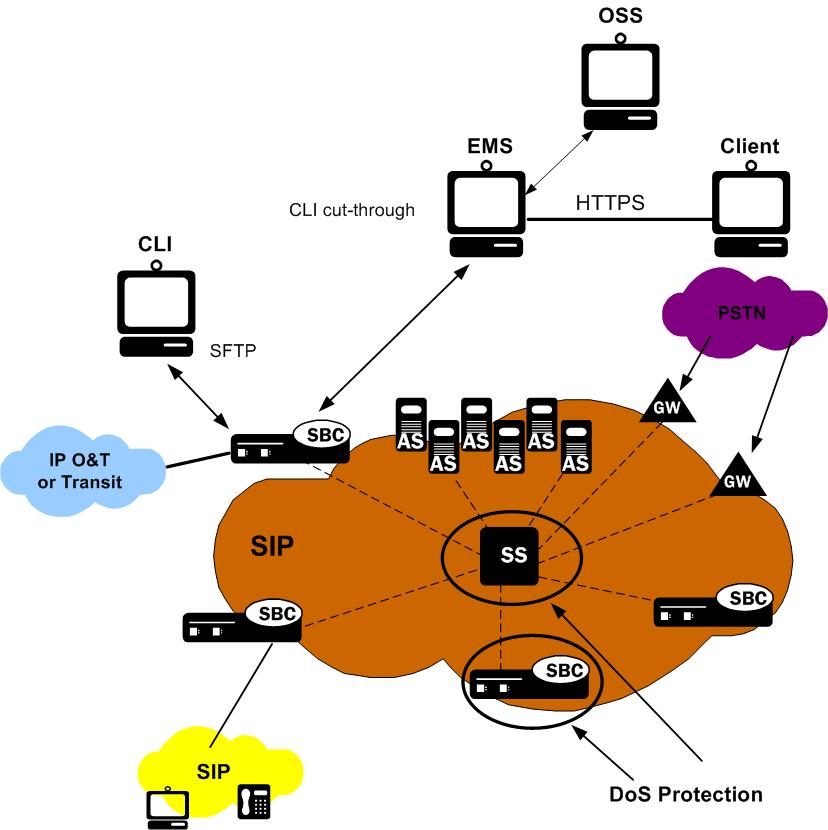
As we can see from the illustration, G Router Denial Of Service (Dos) Protection Setup has many fascinating aspects to explore.
G Router Denial of Service (DoS) Protection Setup works by analyzing traffic patterns and filtering out traffic that is deemed to be malicious. This can include traffic that is coming from multiple sources, traffic that is using suspicious protocols, or traffic that is being sent to a specific server or network.
Configuring G Router Denial of Service (DoS) Protection Setup
Configuring G Router Denial of Service (DoS) Protection Setup is a relatively straightforward process that can be completed in a few simple steps.
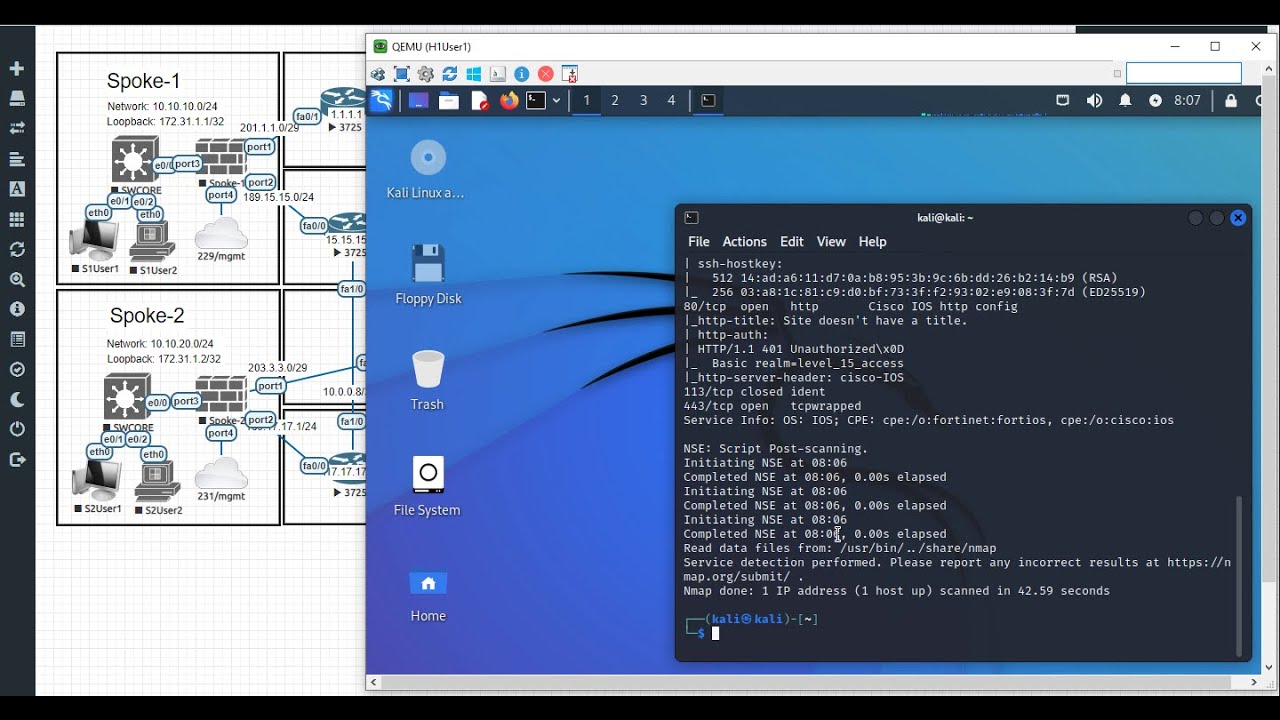
First, access your router settings through your web browser. This is typically done by typing the router's IP address into the address bar and logging in with your username and password.
Once you are logged in, navigate to the security settings page and locate the Denial of Service (DoS) Protection feature. This feature is usually located in the advanced security settings.
Click on the Denial of Service (DoS) Protection feature and select the level of protection you want to enable. The level of protection you choose will depend on your network's specific needs and the type of traffic you expect to be entering the network.
Click on the "Apply" or "Save" button to save your changes. Your router will then begin to scan traffic for malicious activity and filter out any traffic that is deemed to be suspicious.

Tips for Optimizing G Router Denial of Service (DoS) Protection Setup
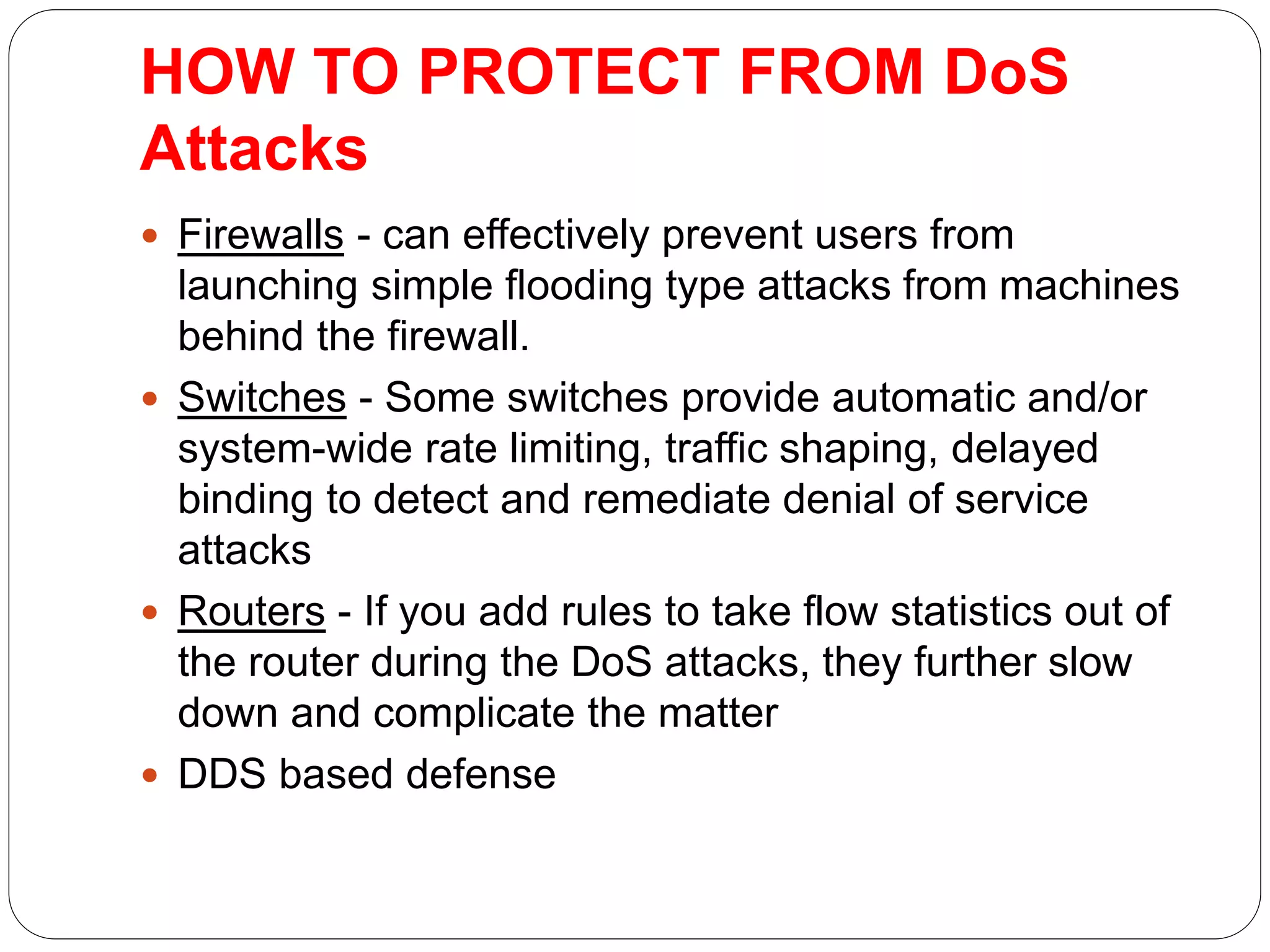
In order to optimize your G Router Denial of Service (DoS) Protection Setup, consider the following tips:
Customize your access lists to allow or block traffic from specific IP addresses or ports. This can help to prevent malicious traffic from entering the network.
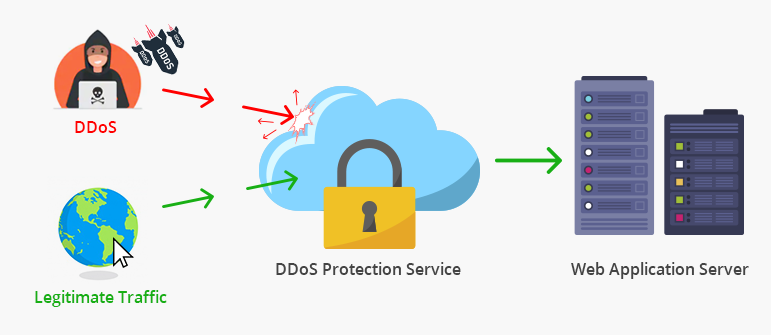
Consider implementing a Distributed Denial of Service (DDoS) protection setup to protect against large-scale attacks.
Regularly update your router's security settings to ensure that you have the latest protection against emerging threats.
Consider using a cloud-based security solution that can provide additional protection against DoS attacks.
Conclusion

By following the steps outlined in this article, you can configure your G Router Denial of Service (DoS) Protection Setup and optimize it for optimal performance. Remember to customize your access lists, implement DDoS protection, and regularly update your router's security settings to ensure that you have the latest protection against emerging threats.
There are several security solutions available that can provide additional protection against DoS attacks. Some of the top solutions include:
FAQs
Here are some frequently asked questions about G Router Denial of Service (DoS) Protection Setup:
Q: What is a DoS attack? A: A DoS attack is a type of cyber attack where an attacker intentionally floods a network with traffic in order to render it unavailable to legitimate users.
Q: How do I prevent a DoS attack? A: You can prevent a DoS attack by configuring your G Router Denial of Service (DoS) Protection Setup to filter out malicious traffic and ensure that only legitimate traffic is allowed to enter the network.
Q: What is a DDoS attack? A: A DDoS attack is a type of cyber attack where an attacker intentionally floods a network with traffic from multiple sources in order to render it unavailable to legitimate users.
Q: How do I configure my G Router Denial of Service (DoS) Protection Setup? A: You can configure your G Router Denial of Service (DoS) Protection Setup by accessing your router settings through your web browser and navigating to the security settings page.








.jpg)