Managing Remote Team Cybersecurity Risks: A Comprehensive Guide
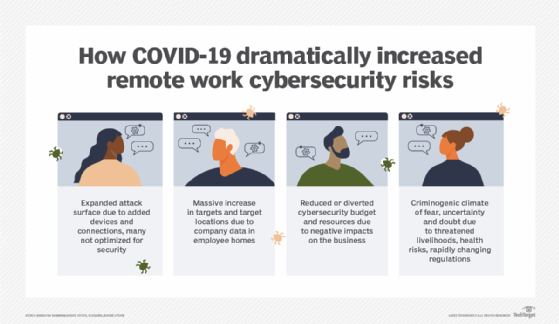
The shift to remote and hybrid work has transformed the way organizations operate, introducing unique cybersecurity challenges that the C-suite must address. As employees access corporate networks from various locations, often using personal devices such as cellphones, the risk of cyber attacks and data breaches increases significantly.
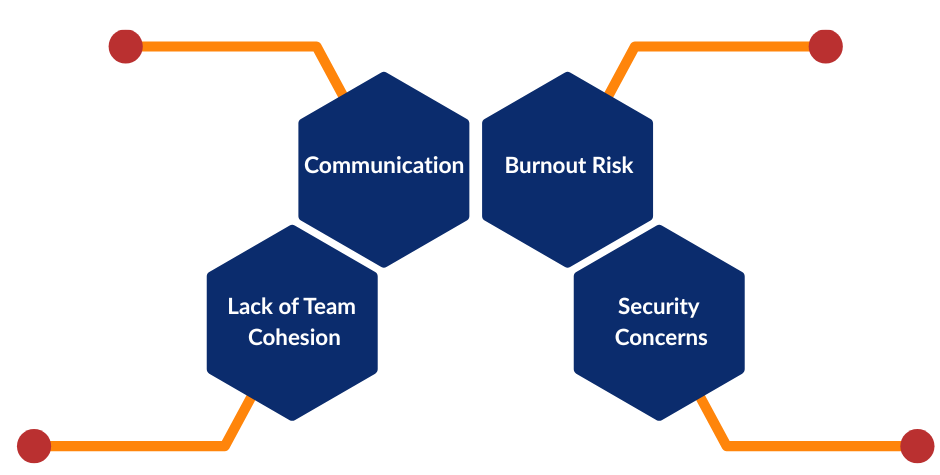
Common Security Risks for Remote and Hybrid Workforces
Managing Remote Team Cybersecurity Risks: Strategies and Solutions

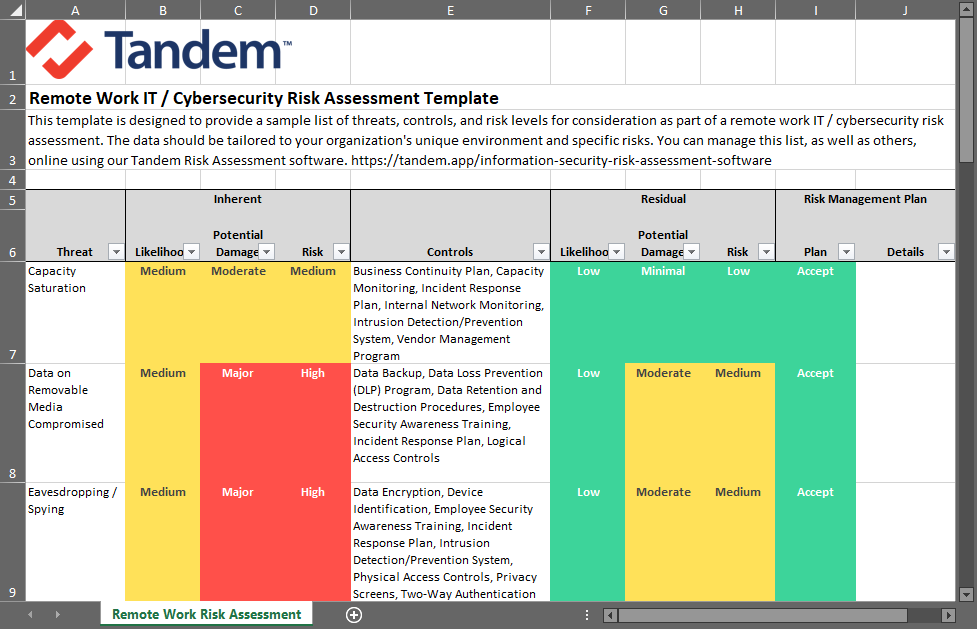
Furthermore, visual representations like the one above help us fully grasp the concept of Managing Remote Team Cybersecurity Risks.
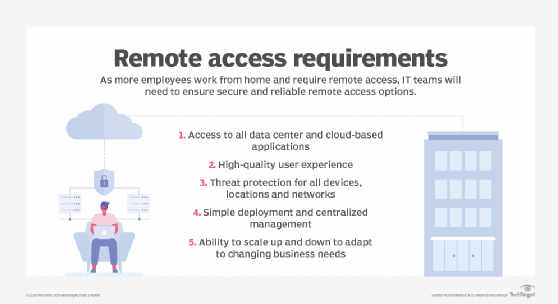
- Centralized Management and Access Controls: Implementing centralized management and access controls allows businesses to monitor and control access in real-time, reducing the risk of unauthorized breaches.
- Cyber Hygiene Practices: Implementing consistent, proactive cyber hygiene practices, such as regular software updates, antivirus scans, and password management, can help reduce the risk of cyber attacks.
- Secure Device Management: Implementing secure device management policies, including remote wipe and lock, can help protect sensitive data in case devices are lost or stolen.
- Cloud Security: Implementing cloud security measures, such as encryption and access controls, can help protect sensitive data in the cloud.
- Regular Training and Awareness Programs: Regular training and awareness programs can help employees understand cybersecurity best practices and recognize potential security threats.
Conclusion
Managing remote team cybersecurity risks requires a comprehensive approach that involves implementing robust security measures, policies, and regular training and awareness programs. By understanding the common security risks associated with remote work and implementing the right strategies and solutions, organizations can safeguard their sensitive data and systems from evolving cyber threats.
Best Practices for Managing Remote Team Cybersecurity Risks
- Implement centralized management and access controls to monitor and control access in real-time.
- Implement cyber hygiene practices, such as regular software updates and antivirus scans.
- Implement secure device management policies, including remote wipe and lock.
- Implement cloud security measures, such as encryption and access controls.
- Regularly train and aware employees on cybersecurity best practices and potential security threats.