Prevent Data Breaches: Top Strategies for a Secure Tomorrow
Understanding the Risks of Data Breaches
In today's digital age, data breaches have become a significant concern for organizations and individuals alike. A data breach occurs when unauthorized access to sensitive information is gained, putting your business's reputation and bottom line at risk. In this article, we'll explore 10 actionable ways to prevent data breaches and safeguard your organization's most valuable assets. When a data breach occurs, it can result in the loss or theft of sensitive data, as well as serious or permanent damage to your system. This can lead to a loss of customer trust, a damaged reputation, and a long-lasting impact on your business. In today's interconnected world, data breaches can spread quickly, affecting not just your organization but also your customers, partners, and stakeholders.Prevent Data Breaches with Encryption

This particular example perfectly highlights why Prevent Data Breaches is so captivating.
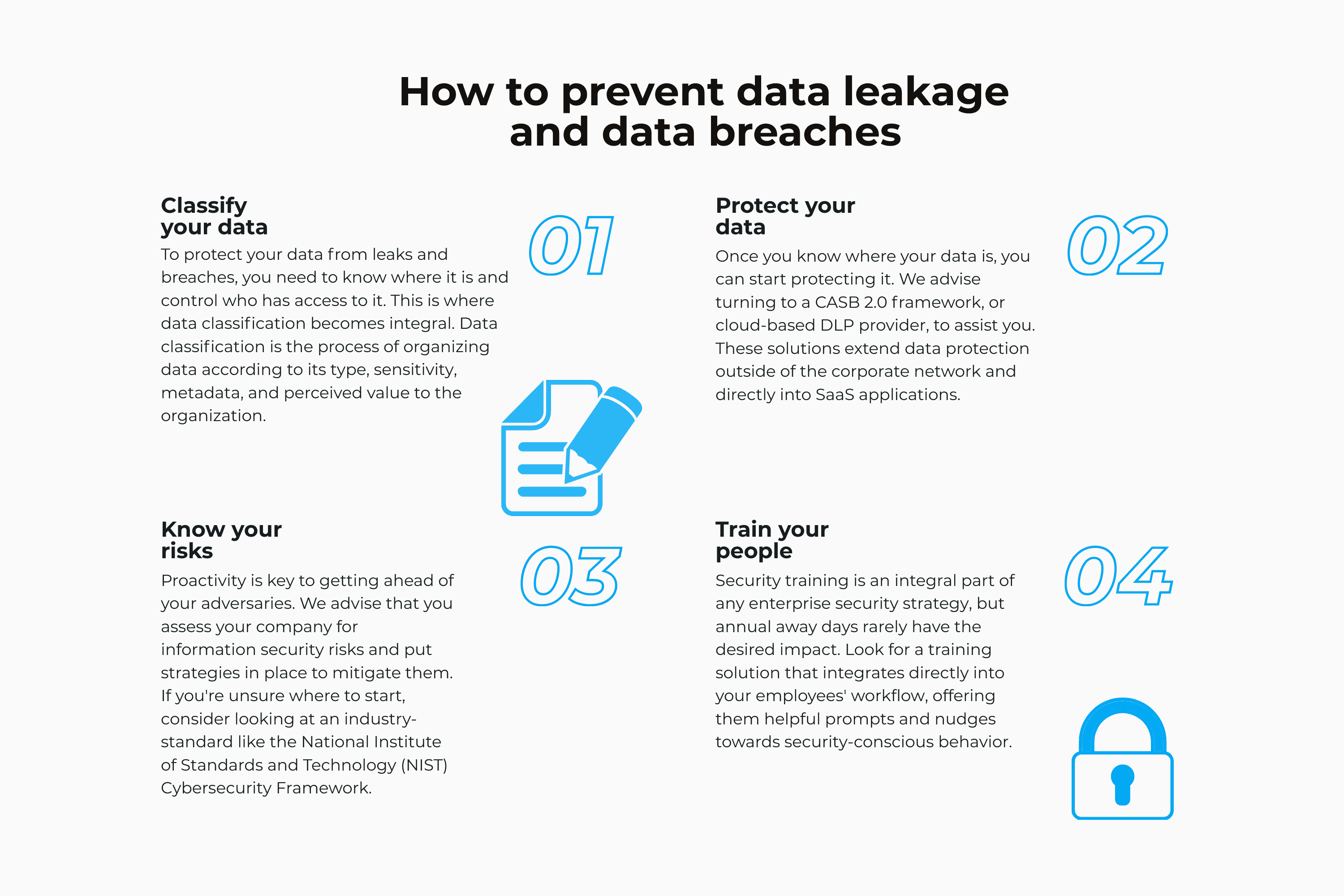
Encryption is a powerful tool for preventing data breaches. By encrypting sensitive data, you can ensure that even if a breach occurs, the data remains secure and cannot be accessed by unauthorized individuals. Implementing encryption across all sensitive systems and data is a crucial step in shoring up your organization's security.Implement Multi-Factor Authentication
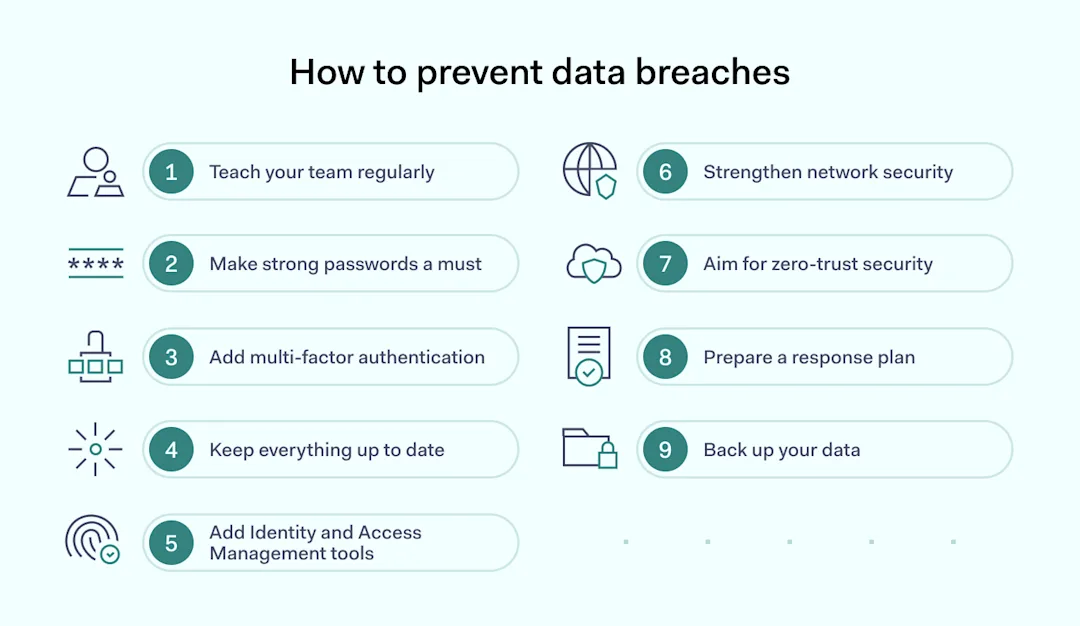
Multi-factor authentication is a simple yet effective way to prevent data breaches. By requiring users to provide multiple forms of verification, you can ensure that only authorized individuals have access to sensitive data and systems. This can include passwords, smart cards, biometric data, and more.Regular Audits and Risk Assessments

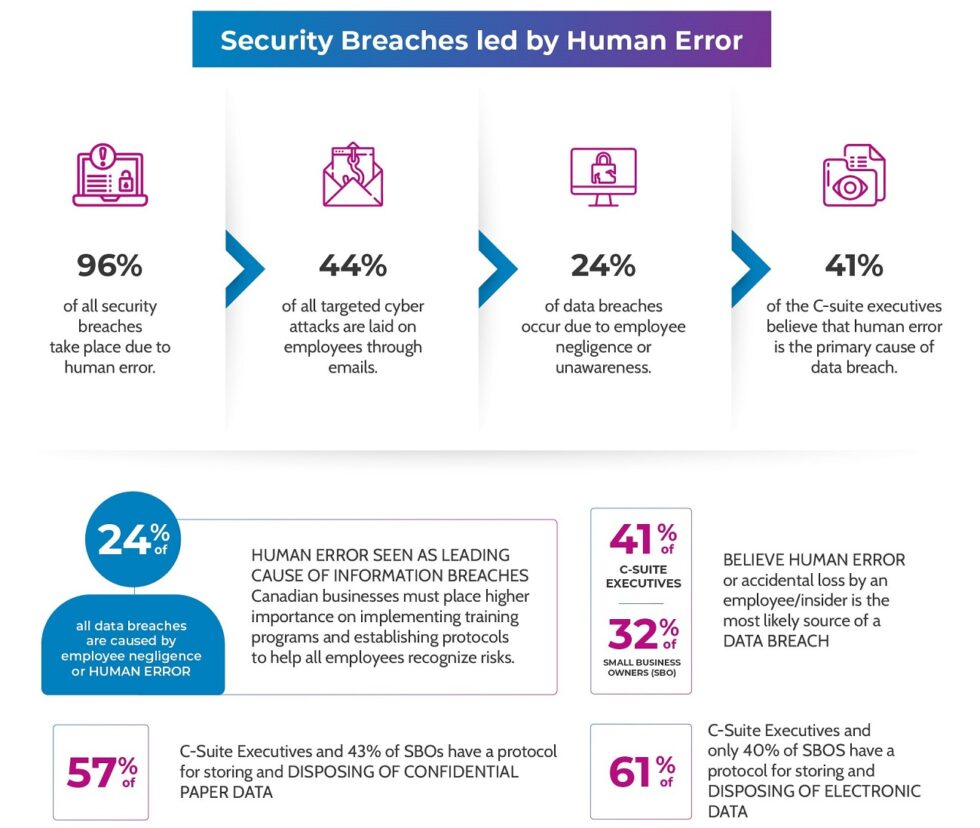
Employee Training and Education
Your employees are often the first line of defense against data breaches. By providing regular training and education on data security best practices, you can empower them to make informed decisions about data handling and security. This can include training on password management, phishing scams, and social engineering tactics.Access Controls and Permissions