Safeguarding Your Phone from Hackers: A Comprehensive Guide
Your phone is an indispensable part of your life, storing sensitive personal data and serving as a gateway to your online presence. However, with the increasing number of cyber threats and hacking incidents, it's essential to take proactive measures to safeguard your phone from hackers. In this article, we'll explore the best practices and expert tips to protect your device from hacking, theft, and unauthorized access.Why is Safeguarding Your Phone from Hackers Crucial?
If your phone falls into the wrong hands, a hacker could gain access to your online accounts, steal your personal data, and even use your device to commit financial fraud. In fact, a recent study revealed that over 1 in 5 smartphones are vulnerable to hacking, making it essential to prioritize phone security. By safeguarding your phone, you can prevent: * Unauthorized access to your personal data and online accounts * Financial loss and identity theft * Malware and ransomware attacks that can compromise your device's integrity * Phishing scams and other online threats that can compromise your online safetyStep 1: Use a Strong PIN or Passcode
* Use a unique and complex passcode that's difficult to guess * Avoid using easily guessable information such as your birthdate or anniversary * Enable fingerprint or facial recognition for an added layer of securityStep 2: Enable Two-Factor Authentication (2FA)

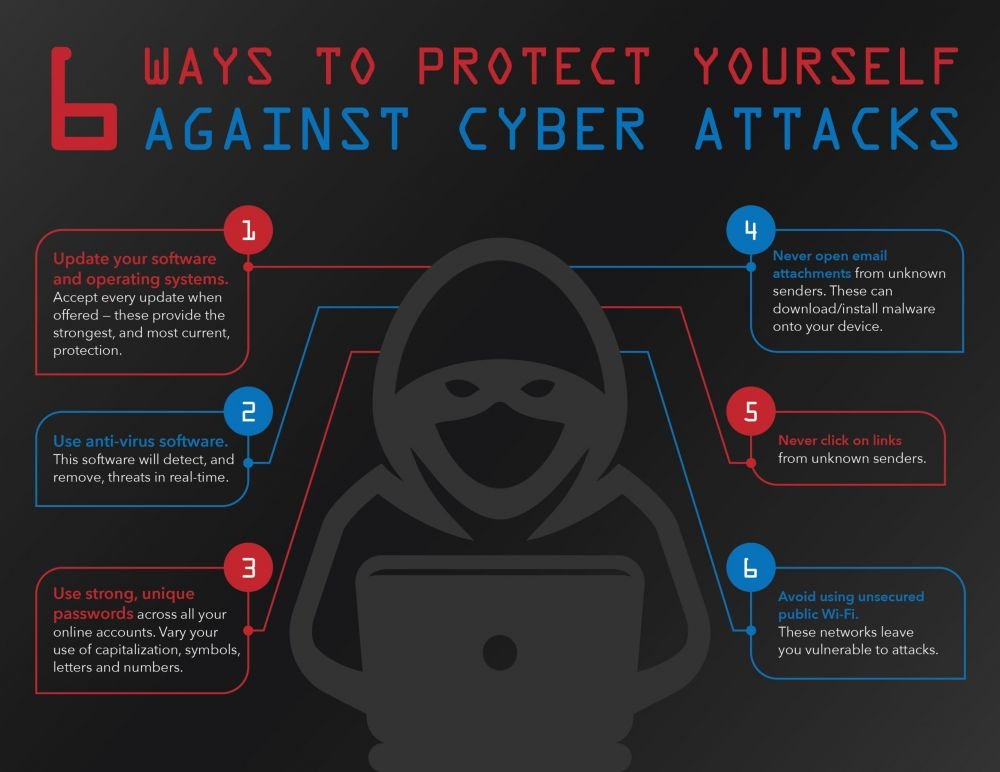
Step 3: Install Anti-Virus Software
* Choose a reputable anti-virus app that's specifically designed for mobile devices * Keep your anti-virus software up-to-date to protect against new threatsStep 4: Be Cautious of Public Wi-Fi
* Avoid using public Wi-Fi networks for sensitive transactions or browsing * Use a Virtual Private Network (VPN) to encrypt your internet trafficStep 5: Use Strong Passwords
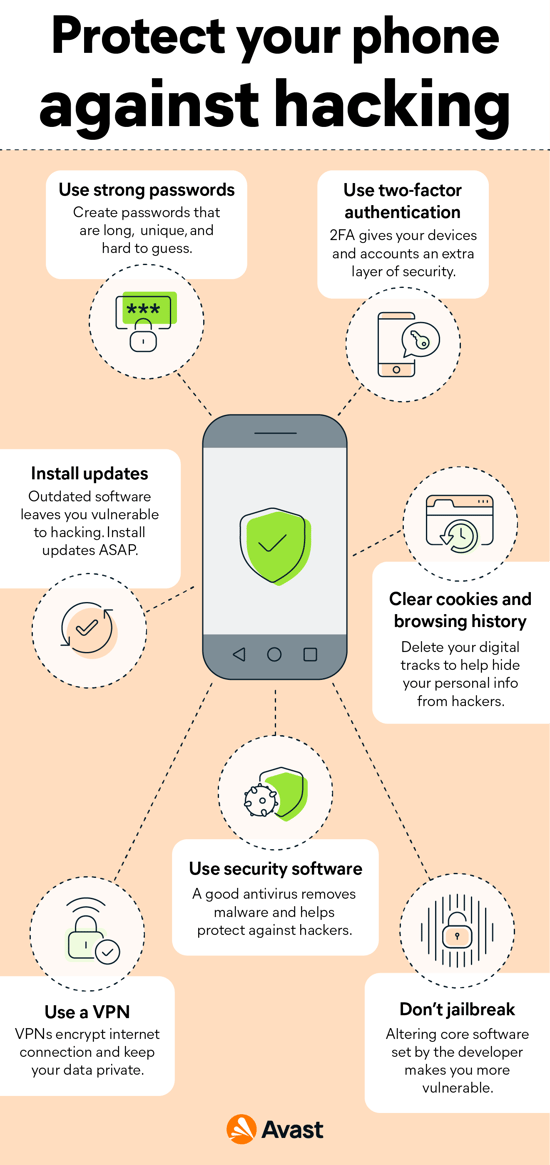
Step 6: Regularly Update Your Device and Apps
* Regularly update your device's operating system and apps to patch security vulnerabilities * Enable automatic updates to ensure you never miss a critical patchStep 7: Use a Secure Browser
* Use a reputable and secure web browser that offers built-in security features * Avoid using public computers or unsecured browsers for sensitive transactionsStep 8: Use a VPN on Public Networks